“Secrets of the Little Blue Box”
The 1971 article about phone hacking that inspired Steve Jobs.
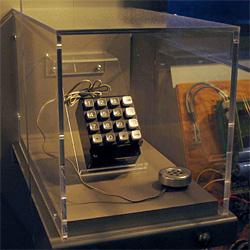
Photograph by RaD man/GFDL/Wikipedia
In 1971, Slate columnist Ron Rosenbaum wrote an article for Esquire about a loose confederation of proto-hackers who built devices—little blue boxes—that could crack phone networks. According the New York Times obituary of Apple founder Steve Jobs, after reading Rosenbaum’s article, Jobs and his partner in founding Apple, Steve Wozniak, “collaborated on building and selling blue boxes, devices that were widely used for making free—and illegal—phone calls. They raised a total of $6,000 from the effort.” The original 1971 article, “Secrets of the Little Blue Box,” is reprinted below, with permission from the author. It’s also available in Rosenbaum’s collection The Secret Parts of Fortune. Also in Slate: Rosenbaum reflects on the article that inspired Steve Jobs.
In Which We Explore the Web of the Original Hackers
There is an underground telephone network in this country. Al Gilbertson (I’ve changed his name) discovered it the day after his arrest for manufacturing illegal “blue boxes.” A crime he is not exactly repentant about. I am sitting in the living room of the creator of the blue box. Gilbertson is holding one of his shiny black-and-silver blue boxes comfortably in the palm of his hand, pointing out the thirteen little red push buttons sticking up from the console. He is dancing his fingers over the buttons, tapping out discordant beeping electronic jingles. He is trying to explain to me how his little blue box does nothing less than place the entire telephone system of the world, satellites, cables and all, at the service of the blue-box operator, free of charge.
“Essentially it gives you the power of a super operator. You seize a tandem with this top button," he presses the top button with his index finger and the blue box emits a high-pitched cheep, "and like that" — cheep goes the blue box again — "you control the phone company's long-distance switching systems from your cute little Princess phone or any old pay phone. And you've got anonymity. An operator has to operate from a definite location: The phone company knows where she is and what she's doing. But with your beeper box, once you hop onto a trunk, say from a Holiday Inn 800 number, they don't know where you are, or where you're coming from, they don't know how you slipped into their lines and popped up in that 800 number. They don't even know anything illegal is going on. And you can obscure your origins through as many levels as you like. You can call next door by way of White Plains, then over to Liverpool by cable, and then back here by satellite. You can call yourself from one pay phone all the way around the world to a pay phone next to you. And you get your dime back too."
"And they can't trace the calls? They can't charge you?"
"Not if you do it the right way. But you'll find that the free-call thing isn't really as exciting at first as the feeling of power you get from having one of these babies in your hand. I've watched people when they first get hold of one of these things and start using it, and discover they can make connections, set up crisscross and zigzag switching patterns back and forth across the world. They hardly talk to the people they finally reach. They say hello and start thinking of what kind of call to make next. They go a little crazy." He looks down at the neat little package in his palm. His fingers are still dancing, tapping out beeper patterns.
"I think it's something to do with how small my models are. There are lots of blue boxes around, but mine are the smallest and most sophisticated electronically. I wish I could show you the prototype we made for our big syndicate order."
He sighs. "We had this order for a thousand beeper boxes from a syndicate front man in Las Vegas. They use them to place bets coast to coast, keep lines open for hours, all of which can get expensive if you have to pay. The deal was a thousand blue boxes for $300 apiece. Before then we retailed them for $1,500 apiece, but $300,000 in one lump was hard to turn down. We had a manufacturing deal worked out in the Philippines. Everything ready to go. Anyway, the model I had ready for limited mass production was small enough to fit inside a flip-top Marlboro box. It had flush touch panels for a keyboard, rather than these unsightly buttons sticking out. Looked just like a tiny portable radio. In fact, I had designed it with a tiny transistor receiver to get one AM channel so in case the law became suspicious the owner could switch on the radio part, start snapping his fingers, and no one could tell anything illegal was going on. I thought of everything for this model — I had it lined with a band of thermite which could be ignited by radio signal from a tiny button transmitter on your belt, so it could be burned to ashes instantly in case of a bust. It was beautiful. A beautiful little machine. You should have seen the faces on these syndicate guys when they came back after trying it out. They'd hold it in their palm like they never wanted to let it go, and they'd say, 'I can't believe it. I can't believe it.' You probably won't believe it until you try it."
You Can Call Long Distance for Less Than You Think
"You see, a few years ago the phone company made one big mistake," Gilbertson explains two days later in his apartment. "They were careless enough to let some technical journal publish the actual frequencies used to create all their multi-frequency tones. Just a theoretical article some Bell Telephone Laboratories engineer was doing about switching theory, and he listed the tones in passing. At ----- [a well-known technical school] I had been fooling around with phones for several years before I came across a copy of the journal in the engineering library. I ran back to the lab and it took maybe twelve hours from the time I saw that article to put together the first working blue box. It was bigger and clumsier than this little baby, but it worked."
It's all there on public record in that technical journal written mainly by Bell Lab people for other telephone engineers. Or at least it was public. "Just try and get a copy of that issue at some engineering-school library now. Bell has had them all red-tagged and withdrawn from circulation," Gilbertson tells me.
"But it's too late. It's all public now. And once they became public the technology needed to create your own beeper device is within the range of any twelve-year-old kid, any twelve-year-old blind kid, as a matter of fact. And he can do it in less than the twelve hours it took us. Blind kids do it all the time. They can't build anything as precise and compact as my beeper box, but theirs can do anything mine can do."
"How?"
"Okay. About twenty years ago AT&T made a multibillion-dollar decision to operate its entire long-distance switching system on twelve electronically generated combinations of six master tones. Those are the tones you sometimes hear in the background after you've dialed a long-distance number. They decided to use some very simple tones — the tone for each number is just two fixed single-frequency tones played simultaneously to create a certain beat frequency. Like 1300 cycles per second and 900 cycles per second played together give you the tone for digit 5. Now, what some of these phone phreaks have done is get themselves access to an electric organ. Any cheap family home-entertainment organ. Since the frequencies are public knowledge now — one blind phone phreak has even had them recorded in one of those talking books for the blind — they just have to find the musical notes on the organ which correspond to the phone tones. Then they tape them. For instance, to get Ma Bell's tone for the number 1, you press down organ keys F5 and A5 [900 and 700 cycles per second] at the same time. To produce the tone for 2 it's F5 and C6 [1100 and 700 cps]. The phone phreaks circulate the whole list of notes so there's no trial and error anymore."
He shows me a list of the rest of the phone numbers and the two electric organ keys that produce them.
"Actually, you have to record these notes at 3¾ inches-per-second tape speed and double it to 7½ inches-per-second when you play them back, to get the proper tones," he adds.
"So once you have all the tones recorded, how do you plug them into the phone system?"
"Well, they take their organ and their cassette recorder, and start banging out entire phone numbers in tones on the organ, including country codes, routing instructions, 'KP' and 'Start' tones. Or, if they don't have an organ, someone in the phone-phreak network sends them a cassette with all the tones recorded, with a voice saying 'Number one,' then you have the tone, 'Number two,' then the tone, and so on. So with two cassette recorders they can put together a series of phone numbers by switching back and forth from number to number. Any idiot in the country with a cheap cassette recorder can make all the free calls he wants."
"You mean you just hold the cassette recorder up the mouthpiece and switch in a series of beeps you've recorded? The phone thinks that anything that makes these tones must be its own equipment?"
"Right. As long as you get the frequency within thirty cycles per second of the phone company's tones, the phone equipment thinks it hears its own voice talking to it. The original granddaddy phone phreak was this blind kid with perfect pitch, Joe Engressia, who used to whistle into the phone. An operator could tell the difference between his whistle and the phone company's electronic tone generator, but the phone company's switching circuit can't tell them apart. The bigger the phone company gets and the further away from human operators it gets, the more vulnerable it becomes to all sorts of phone phreaking."
"What about the recent series of blue-box arrests all across the country — New York, Cleveland, and so on?" I asked. "How were they caught so easily?"
"From what I can tell, they made one big mistake: They were seizing trunks using an area code plus 555-1212 instead of an 800 number. Using 555 is easy to detect because when you send multifrequency beep tones off 555 you get a charge for it on your tape and the accounting computer knows there's something wrong when it tries to bill you for a two-hour call to Akron, Ohio, information, and it drops a trouble card which goes right into the hands of the security agent if they're looking for blue-box users.
"Whoever sold those guys their blue boxes didn't tell them how to use them properly, which is fairly irresponsible. And they were fairly stupid to use them at home all the time.
"But what those arrests really mean is that an awful lot of blue boxes are flooding into the country and that people are finding them so easy to make that they know how to make them before they know how to use them. Ma Bell is in trouble."
And if a blue-box operator or a cassette-recorder phone phreak sticks to pay phones and 800 numbers, the phone company can't stop them?
"Not unless they change their entire nationwide long-lines technology, which will take them a few billion dollars and twenty years. Right now they can't do a thing. They're screwed."
Captain Crunch Demonstrates His Famous Unit
Al Gilbertson discovered the underground telephone network the very day news of his activities hit the papers. That evening his phone began ringing. Phone phreaks from Seattle, from Florida, from New York, from San Jose, and from Los Angeles began calling him and telling him about the phone-phreak network. He'd get a call from a phone phreak who'd say nothing but, "Hang up and call this number."
When he dialed the number he'd find himself tied into a conference of a dozen phone phreaks arranged through a quirky switching station in British Columbia. They identified themselves as phone phreaks, they demonstrated their homemade blue boxes which they called "M-F-ers" (for "multi-frequency," among other things) for him, they talked shop about phone-phreak devices. They let him in on their secrets on the theory that if the phone company was after him he must be trustworthy. And, Gilbertson recalls, they stunned him with their technical sophistication.
I ask him how to get in touch with the phone-phreak network. He digs around through a file of old schematics and comes up with about a dozen numbers in three widely separated area codes.
"Those are the centers," he tells me. Alongside some of the numbers he writes in first names or nicknames: names like Captain Crunch, Dr. No, Frank Carson (also a code word for a free call), Marty Freeman (code word for M-F device), Peter Perpendicular Pimple, Alefnull, and The Cheshire Cat. He makes checks alongside the names of those among these top twelve who are blind. There are five checks.
I ask him who this Captain Crunch person is.
"Oh. The Captain. He's probably the most legendary phone phreak. He calls himself Captain Crunch after the notorious Cap'n Crunch 2600 whistle." (Several years ago, Gilbertson explains, the makers of Cap'n Crunch breakfast cereal offered a toy-whistle prize in every box as a treat for the Cap'n Crunch set. Somehow a phone phreak discovered that the toy whistle just happened to produce a perfect 2600-cycle tone. When the man who calls himself Captain Crunch was transferred overseas to England with his Air Force unit, he would receive scores of calls from his friends and "mute" them — make them free of charge to them — by blowing his Cap'n Crunch whistle into his end.)
"Captain Crunch is one of the older phone phreaks," Gilbertson tells me. "He's an engineer who once got in a little trouble for fooling around with the phone, but he can't stop. Well, this guy drives across country in a Volkswagen van with an entire switchboard and a computerized super-sophisticated M-F-er in the back. He'll pull up to a phone booth on a lonely highway somewhere, snake a cable out of his bus, hook it onto the phone and sit for hours, days sometimes, sending calls zipping back and forth across the country, all over the world...."
Back at my motel, I dialed the number he gave me for "Captain Crunch" and asked for G---- T-----, his real name, or at least the name he uses when he's not dashing into a phone booth beeping out M-F tones faster than a speeding bullet, and zipping phantomlike through the phone company's long-distance lines.
When G---- T----- answered the phone and I told him I was preparing a story for Esquire about phone phreaks, he became very indignant.
"I don't do that. I don't do that anymore at all. And if I do it, I do it for one reason and one reason only. I'm learning about a system. The phone company is a System. A computer is a System. Do you understand? If I do what I do, it is only to explore a System. Computers. Systems. That's my bag. The phone company is nothing but a computer."
A tone of tightly restrained excitement enters the Captain's voice when he starts talking about Systems. He begins to pronounce each syllable with the hushed deliberation of an obscene caller.
"Ma Bell is a system I want to explore. It's a beautiful system, you know, but Ma Bell screwed up. It's terrible because Ma Bell is such a beautiful system, but she screwed up. I learned how she screwed up from a couple of blind kids who wanted me to build a device. A certain device. They said it could make free calls. I wasn't interested in free calls. But when these blind kids told me I could make calls into a computer, my eyes lit up. I wanted to learn about computers. I wanted to learn about Ma Bell's computers. So I built the little device. Only I built it wrong and Ma Bell found out. Ma Bell can detect things like that. Ma Bell knows. So I'm strictly out of it now. I don't do it. Except for learning purposes." He pauses. "So you want to write an article. Are you paying for this call? Hang up and call this number."
He gives me a number in an area code a thousand miles north of his own. I dial the number.
"Hello again. This is Captain Crunch. You are speaking to me on a toll-free loop-around in Portland, Oregon. Do you know what a toll-free loop around is? I'll tell you."
He explains to me that almost every exchange in the country has open test numbers which allow other exchanges to test their connections with it. Most of these numbers occur in consecutive pairs, such as 302 956-0041 and 956-0042. Well, certain phone phreaks discovered that if two people from anywhere in the country dial those two consecutive numbers they can talk together just as if one had called the other's number, with no charge to either of them, of course.
"Your voice is looping around in a 4A switching machine up there in Canada, zipping back down to me," the Captain tells me. "My voice is looping around up there and back down to you. And it can't ever cost anyone money. The phone phreaks and I have compiled a list of many many of these numbers. You would be surprised if you saw the list. I could show it to you. But I won't. I'm out of that now. I'm not out to screw Ma Bell. I know better. If I do anything it's for the pure knowledge of the System. You can learn to do fantastic things. Have you ever heard eight tandems stacked up? Do you know the sound of tandems stacking and unstacking? Give me your phone number. Okay. Hang up now and wait a minute."
Slightly less than a minute later the phone rang and the Captain was on the line, his voice sounding far more excited, almost aroused.
"I wanted to show you what it's like to stack up tandems. To stack up tandems." (Whenever the Captain says "stack up" it sounds as if he is licking his lips.)
"How do you like the connection you're on now?" the Captain asks me. "It's a raw tandem. A raw tandem. Ain't nothin' up to it but a tandem. Now I'm going to show you what it's like to stack up. Blow off. Land in a far away place. To stack that tandem up, whip back and forth across the country a few times, then shoot on up to Moscow.
"Listen," Captain Crunch continues. "Listen. I've got a line tie on my switchboard here, and I'm gonna let you hear me stack and unstack tandems. Listen to this. It's gonna blow your mind."
First I hear a super rapid-fire pulsing of the flutelike phone tones, then a pause, then another popping burst of tones, then another, then another. Each burst is followed by a beep-kachink sound.
"We have now stacked up four tandems," said Captain Crunch, sounding somewhat remote. "That's four tandems stacked up. Do you know what that means? That means I'm whipping back and forth, back and forth twice, across the country, before coming to you. I've been known to stack up twenty tandems at a time. Now, just like I said, I'm going to shoot up to Moscow."
There is a new, longer series of beeper pulses over the line, a brief silence, then a ring.
"Hello," answers a far-off voice.
"Hello. Is this the American Embassy Moscow?"
"Yes, sir. Who is this calling?" says the voice.
"Yes. This is test board here in New York. We're calling to check out the circuits, see what kind of lines you've got. Everything okay there in Moscow?"
"Okay?"
"Well, yes, how are things there?"
"Oh. Well, everything's okay, I guess."
"Okay. Thank you." They hang up, leaving a confused series of beep-kachink sounds hanging in mid-ether in the wake of the call before dissolving away.
The Captain is pleased. "You believe me now, don't you? Do you know what I'd like to do? I'd like to call up your editor at Esquire and show him just what it sounds like to stack and unstack tandems. I'll give him a show that will blow his mind. What's his number?"
I ask the Captain what kind of device he was using to accomplish all his feats. The Captain is pleased at the question.
"You could tell it was special, couldn't you? Ten pulses per second. That's faster than the phone company's equipment. Believe me, this unit is the most famous unit in the country. There is no other unit like it. Believe me."
"Yes, I've heard about it. Some other phone phreaks have told me about it."
"They have been referring to my, ahem, unit? What is it they said? Just out of curiosity, did they tell you it was a highly sophisticated computer-operated unit, with acoustical coupling for receiving outputs and a switch-board with multiple-line capability? Did they tell you that the frequency tolerance is guaranteed to be not more than .05 percent? The amplitude tolerance less than .01 decibel? Those pulses you heard were perfect. They just come faster than the phone company. Those were high-precision op-amps. Op-amps are instrumentation amplifiers designed for ultra-stable amplification, super-low distortion, and accurate frequency response. Did they tell you it can operate in temperatures from minus 55 degrees centigrade to plus 125 degrees centigrade?"
I admit that they did not tell me all that.
"I built it myself," the Captain goes on. "If you were to go out and buy the components from an industrial wholesaler it would cost you at least $1,500. I once worked for a semiconductor company and all this didn't cost me a cent. Do you know what I mean? Did they tell you about how I put a call completely around the world? I'll tell you how I did it. I M-F-ed Tokyo inward, who connected me to India, India connected me to Greece, Greece connected me to Pretoria, South Africa, South Africa connected me to South America, I went from South America to London, I had a London operator connect me to a New York operator, I had New York connect me to a California operator, who rang the phone next to me. Needless to say I had to shout to hear myself. But the echo was far out. Fantastic. Delayed. It was delayed twenty seconds, but I could hear myself talk to myself."
"You mean you were speaking into the mouthpiece of one phone sending your voice around the world into your ear through a phone on the other side of your head?" I asked the Captain. I had a vision of something vaguely autoerotic going on, in a complex electronic way.
"That's right," said the Captain. "I've also sent my voice around the world one way, going east on one phone, and going west on the other, going through cable one way, satellite the other, coming back together at the same time, ringing the two phones simultaneously and picking them up and whipping my voice both ways around the world back to me. Wow. That was a mind blower."
"You mean you sit there with both phones on your ear and talk to yourself around the world," I said incredulously.
"Yeah. Um hum. That's what I do. I connect the phones together and sit there and talk."
"What do you say? What do you say to yourself when you're connected?"
"Oh, you know. Hello test one two three," he says in a low-pitched voice.
"Hello test one two three," he replied to himself in a high-pitched voice.
"Hello test one two three," he repeats again, low-pitched.
"Hello test one two three," he replies, high-pitched.
"I sometimes do this: Hello hello hello hello, hello, hello," he trails off and breaks into laughter.
Why Captain Crunch Hardly Ever Taps Phones Anymore
Using internal phone-company codes, phone phreaks have learned a simple method for tapping phones. Phone-company operators have in front of them a board that holds verification jacks. It allows them to plug into conversations in case of emergency, to listen in to a line to determine if the line is busy or the circuits are busy. Phone phreaks have learned to beep out the codes which lead them to a verification operator, tell the verification operator they are switchmen from some other area code testing out verification trunks. Once the operator hooks them into the verification trunk, they disappear into the board for all practical purposes, slip unnoticed into any one of the 10,000 to 100,000 numbers in that central office without the verification operator knowing what they're doing, and of course without the two parties to the connection knowing there is a phantom listener present on their line.
Toward the end of my hour-long first conversation with him, I asked the Captain if he ever tapped phones.
"Oh no. I don't do that. I don't think it's right," he told me firmly. "I have the power to do it but I don't... Well one time, just one time, I have to admit that I did. There was this girl, Linda, and I wanted to find out... you know. I tried to call her up for a date. I had a date with her the last weekend and I thought she liked me. I called her up, man, and her line was busy, and I kept calling and it was still busy. Well, I had just learned about this system of jumping into lines and I said to myself, 'Hmmm. Why not just see if it works. It'll surprise her if all of a sudden I should pop up on her line. It'll impress her, if anything.' So I went ahead and did it. I M-F-ed into the line. My M-F-er is powerful enough when patched directly into the mouthpiece to trigger a verification trunk without using an operator the way the other phone phreaks have to.
"I slipped into the line and there she was talking to another boyfriend. Making sweet talk to him. I didn't make a sound because I was so disgusted. So I waited there for her to hang up, listening to her making sweet talk to the other guy. You know. So as soon as she hung up I instantly M-F-ed her up and all I said was, 'Linda, we're through.' And I hung up. And it blew her head off. She couldn't figure out what the hell happened.
"But that was the only time. I did it thinking I would surprise her, impress her. Those were all my intentions were, and well, it really kind of hurt me pretty badly, and... and ever since then I don't go into verification trunks."
Moments later my first conversation with the Captain comes to a close.
"Listen," he says, his spirits somewhat cheered, "listen. What you are going to hear when I hang up is the sound of tandems unstacking. Layer after layer of tandems unstacking until there's nothing left of the stack, until it melts away into nothing. Cheep, cheep, cheep, cheep," he concludes, his voice descending to a whisper with each cheep.
He hangs up. The phone suddenly goes into four spasms: kachink cheep. Kachink cheep kachink cheep kachink cheep, and the complex connection has wiped itself out like the Cheshire cat's smile.
The MF Boogie Blues
The next number I choose from the select list of phone-phreak illuminati, prepared for me by the blue-box inventor is a Memphis number. It is the number of Joe Engressia, the first and still perhaps the most accomplished blind phone phreak.
Three years ago Engressia was a nine-day wonder in newspapers and magazines all over America because he had been discovered whistling free long-distance connections for fellow students at the University of South Florida. Engressia was born with perfect pitch; he could whistle phone tones better than the phone-company's equipment.
Engressia might have gone on whistling in the dark for a few friends for the rest of his life if the phone company hadn't decided to expose him. He was warned, disciplined by the college, and the whole case became public. In the months following media reports of his talent, Engressia began receiving strange calls. There were calls from a group of kids in Los Angeles who could do some very strange things with the quirky General Telephone and Electronics circuitry in L.A. suburbs. There were calls from a group of mostly blind kids in ----, California, who had been doing some interesting experiments with Cap'n Crunch whistles and test loops. There was a group in Seattle, a group in Cambridge, Massachusetts, a few from New York, a few scattered across the country. Some of them had already equipped themselves with cassette and electronic M-F devices. For some of these groups, it was the first time they knew of the others.
The exposure of Engressia was the catalyst that linked the separate phone-phreak centers together. They all called Engressia. They talked to him about what he was doing and what they were doing. And then he told them — the scattered regional centers and lonely independent phone phreakers — about each other, gave them each other's numbers to call, and within a year the scattered phone-phreak centers had grown into a nationwide underground.
Joe Engressia is only twenty-two years old now, but along the phone-phreak network he is "the old man," accorded by phone phreaks something of the reverence the phone company bestows on Alexander Graham Bell. He seldom needs to make calls anymore. The phone phreaks all call him and let him know what new tricks, new codes, new techniques they have learned. Every night he sits like a sightless spider in his little apartment receiving messages from every tendril of his web. It is almost a point of pride with Joe that they call him.
But when I reached him in his Memphis apartment that night, Joe Engressia was lonely, jumpy and upset.
"God, I'm glad somebody called. I don't know why tonight of all nights I don't get any calls. This guy around here got drunk again tonight and propositioned me again. I keep telling him we'll never see eye to eye on this subject, if you know what I mean. I try to make light of it, you know, but he doesn't get it. I can hear him out there getting drunker and I don't know what he'll do next. It's just that I'm really all alone here. I just moved to Memphis, it's the first time I'm living out on my own, and I'd hate for it to all collapse now. But I won't go to bed with him. I'm just not very interested in sex and even if I can't see him I know he's ugly.
"Did you hear that? That's him banging a bottle against the wall outside. He's nice. Well forget about it. You're doing a story on phone phreaks? Listen to this. It's the M F Boogie blues."
Sure enough, a jumpy version of “Muskrat Ramble” boogies its way over the line, each note one of those long-distance phone tones. The music stops. A huge roaring voice blasts the phone off my ear: "AND THE QUESTION IS..." roars the voice, "CAN A BLIND PERSON HOOK UP AN AMPLIFIER ON HIS OWN?"
The roar ceases. A high-pitched operator-type voice replaces it. "This is Southern Braille Tel. & Tel. Have tone, will phone."
This is succeeded by a quick series of M-F tones, a swift "kachink" and a deep reassuring voice: "If you need home care, call the visiting-nurses association. First National time in Honolulu is four thirty-two p.m."
Joe back in his Joe voice again: "Are we seeing eye to eye? 'Sí, sí,' said the blind Mexican. Ahem. Yes. Would you like to know the weather in Tokyo?"
This swift manic sequence of phone-phreak vaudeville stunts and blind-boy jokes manages to keep Joe's mind off his tormentor only as long as it lasts.
"The reason I'm in Memphis, the reason I have to depend on that homosexual guy, is that this is the first time I've been able to live on my own and make phone trips on my own. I've been banned from all central offices around home in Florida, they knew me too well, and at the University some of my fellow scholars were always harassing me because I was on the dorm pay phone all the time and making fun of me because of my fat ass, which of course I do have, it's my physical fatness program, but I don't like to hear it every day, and if I can't phone trip and I can't phone phreak, I can't imagine what I'd do, I've been devoting three quarters of my life to it.
"I moved to Memphis because I wanted to be on my own as well as because it has a Number 5 crossbar switching system and some interesting little independent phone-company districts nearby and so far they don't seem to know who I am so I can go on phone tripping, and for me phone tripping is just as important as phone phreaking."
Phone tripping, Joe explains, begins with calling up a central-office switch room. He tells the switchman in a polite earnest voice that he's a blind college student interested in telephones, and could he perhaps have a guided tour of the switching station? Each step of the tour Joe likes to touch and feel relays, caress switching circuits, switchboards, crossbar arrangements.
So when Joe Engressia phone phreaks he feels his way through the circuitry of the country garden of forking paths, he feels switches shift, relays shunt, crossbars swivel, tandems engage and disengage even as he hears — with perfect pitch — his M-F pulses make the entire Bell system dance to his tune.
Just one month ago Joe took all his savings out of his bank and left home, over the emotional protests of his mother. "I ran away from home almost," he likes to say. Joe found a small apartment house on Union Avenue and began making phone trips. He'd take a bus a hundred miles south into Mississippi to “see” some old-fashioned Bell equipment still in use in several states, which had been puzzling him. He'd take a bus three hundred miles to Charlotte, North Carolina, to get a feel for some brand-new experimental equipment. He hired a taxi to drive him twelve miles to a suburb to tour the office of a small phone company with some interesting idiosyncrasies in its routing system. He was having the time of his life, he said, the most freedom and pleasure he had known.
In that month he had done very little long-distance phone phreaking from his own phone. He had begun to apply for a job with the phone company, he told me, and he wanted to stay away from anything illegal.
"Any kind of job will do, anything as menial as the most lowly operator. That's probably all they'd give me because I'm blind. Even though I probably knew more than most switchmen. But that's okay. I want to work for Ma Bell. I don't hate Ma Bell the way Gilbertson and some phone phreaks do. I don't want to screw Ma Bell. With me it's the pleasure of pure knowledge. There's something beautiful about the system when you know it intimately the way I do. But I don't know how much they know about me here. I have a very intuitive feel for the condition of the line I'm on, and I think they're monitoring me off and on lately, but I haven't been doing much illegal. I have to make a few calls to switchmen once in a while which aren't strictly legal, and once I took an acid trip and was having these auditory hallucinations as if I were trapped and these planes were dive-bombing me, and all of sudden I had to phone phreak out of there. For some reason I had to call Kansas City, but that's all."
A Warning Is Delivered
At this point — one o'clock in my time zone — a loud knock on my motel-room door interrupts our conversation. Outside the door I find a uniformed security guard who informs me that there has been an "emergency phone call" for me while I have been on the line and that the front desk has sent him up to let me know.
Two seconds after I say good-bye to Joe and hang up, the phone rings.
"Who were you talking to?" the agitated voice demands. The voice belongs to Captain Crunch. "I called because I decided to warn you of something. I decided to warn you to be careful. I don't want this information you get to get to the radical underground. I don't want it to get into the wrong hands. What would you say if I told you it's possible for three phone phreaks to saturate the phone system of the nation? Saturate it. Busy it out. All of it. I know how to do this. I'm not gonna tell. A friend of mine has already saturated the trunks between Seattle and New York. He did it with a computerized M-F-er hitched into a special Manitoba exchange. But there are other, easier ways to do it."
Just three people? I ask. How is that possible?
"Have you ever heard of the long-lines guard frequency? Do you know about stacking tandems with 17 and 2600? Well, I'd advise you to find out about it. I'm not gonna tell you. But whatever you do, don't let this get into the hands of the radical underground."
(Later Gilbertson the inventor confessed that while he had always been skeptical about the Captain's claim of the sabotage potential of trunk-tying phone phreaks, he had recently heard certain demonstrations which convinced him the Captain was not speaking idly. "I think it might take more than three people, depending on how many machines like Captain Crunch's were available. But even though the Captain sounds a little weird, he generally turns out to know what he's talking about.")
"You know," Captain Crunch continues in his admonitory tone, "you know the younger phone phreaks call Moscow all the time. Suppose everybody were to call Moscow. I'm no right-winger. But I value my life. I don't want the Commies coming over and dropping a bomb on my head. That's why I say you've got to be careful about who gets this information."
The Captain suddenly shifts into a diatribe against those phone phreaks who don't like the phone company.
"They don't understand, but Ma Bell knows everything they do. Ma Bell knows. Listen, is this line hot? I just heard someone tap in. I'm not paranoid, but I can detect things like that. Well, even if it is, they know that I know that they know that I have a bulk eraser. I'm very clean." The Captain pauses, evidently torn between wanting to prove to the phone-company monitors that he does nothing illegal, and the desire to impress Ma Bell with his prowess. "Ma Bell knows the things I can do," he continues. "Ma Bell knows how good I am. And I am quite good. I can detect reversals, tandem switching, everything that goes on on a line. I have relative pitch now. Do you know what that means? My ears are a $20,000 piece of equipment. With my ears I can detect things they can't hear with their equipment. I've had employment problems. I've lost jobs. But I want to show Ma Bell how good I am. I don't want to screw her, I want to work for her. I want to do good for her. I want to help her get rid of her flaws and become perfect. That's my number-one goal in life now." The Captain concludes his warnings and tells me he has to be going. "I've got a little action lined up for tonight," he explains and hangs up.
Before I hang up for the night, I call Joe Engressia back. He reports that his tormentor has finally gone to sleep — "He's not blind drunk, that's the way I get, ahem, yes; but you might say he's in a drunken stupor." I make a date to visit Joe in Memphis in two days.
A Phone Phreak Cell Takes Care of Business
The next morning I attend a gathering of four phone phreaks in ----- (a California suburb). The gathering takes place in a comfortable split-level home in an upper-middle-class subdivision. Heaped on the kitchen table are the portable cassette recorders, M-F cassettes, phone patches, and line ties of the four phone phreaks present. On the kitchen counter next to the telephone is a shoe-box-size blue box with thirteen large toggle switches for the tones. The parents of the host phone phreak, Ralph, who is blind, stay in the living room with their sighted children. They are not sure exactly what Ralph and his friends do with the phone or if it's strictly legal, but he is blind and they are pleased he has a hobby which keeps him busy.
The group has been working at reestablishing the historic "2111" conference, reopening some toll-free loops, and trying to discover the dimensions of what seem to be new initiatives against phone phreaks by phone-company security agents.
It is not long before I get a chance to see, to hear, Randy at work. Randy is known among the phone phreaks as perhaps the finest con man in the game. Randy is blind. He is pale, soft and pear-shaped, he wears baggy pants and a wrinkly nylon white sport shirt, pushes his head forward from hunched shoulders somewhat like a turtle inching out of its shell. His eyes wander, crossing and recrossing, and his forehead is somewhat pimply. He is only sixteen years old.
But when Randy starts speaking into a telephone mouthpiece his voice becomes so stunningly authoritative it is necessary to look again to convince yourself it comes from a chubby adolescent Randy. Imagine the voice of a crack oil-rig foreman, a tough, sharp, weather-beaten Marlboro man of forty. Imagine the voice of a brilliant performance-fund gunslinger explaining how he beats the Dow Jones by thirty percent. Then imagine a voice that could make those two sound like Stepin Fetchit. That is sixteen-year-old Randy's voice.
He is speaking to a switchman in Detroit. The phone company in Detroit had closed up two toll-free loop pairs for no apparent reason, although heavy use by phone phreaks all over the country may have been detected. Randy is telling the switchman how to open up the loop and make it free again:
"How are you, buddy. Yeah. I'm on the board in here in Tulsa, Oklahoma, and we've been trying to run some tests on your loop-arounds and we find'em busied out on both sides.... Yeah, we've been getting a 'BY' on them, what d'ya say, can you drop cards on 'em? Do you have 08 on your number group? Oh that's okay, we've had this trouble before, we may have to go after the circuit. Here lemme give 'em to you: your frame is 05, vertical group 03, horizontal 5, vertical file 3. Yeah, we'll hang on here.... Okay, found it? Good. Right, yeah, we'd like to clear that busy out. Right. All you have to do is look for your key on the mounting plate, it's in your miscellaneous trunk frame. Okay? Right. Now pull your key from NOR over the LET. Yeah. I don't know why that happened, but we've been having trouble with that one. Okay. Thanks a lot fella. Be seein' ya."
Randy hangs up, reports that the switchman was a little inexperienced with the loop-around circuits on the miscellaneous trunk frame, but that the loop has been returned to its free-call status.
Delighted, phone phreak Ed returns the pair of numbers to the active-status column in his directory. Ed is a superb and painstaking researcher. With almost Talmudic thoroughness he will trace tendrils of hints through soft-wired mazes of intervening phone-company circuitry back through complex linkages of switching relays to find the location and identity of just one toll-free loop. He spends hours and hours, every day, doing this sort of thing. He has somehow compiled a directory of eight hundred "Band-six in-WATS numbers" located in over forty states. Band-six in-WATS numbers are the big 800 numbers — the ones that can be dialed into free from anywhere in the country.
Ed the researcher, a nineteen-year-old engineering student, is also a superb technician. He put together his own working blue box from scratch at age seventeen. (He is sighted.) This evening after distributing the latest issue of his in-WATS directory (which has been typed into Braille for the blind phone phreaks), he announces he has made a major new breakthrough:
"I finally tested it and it works, perfectly. I've got this switching matrix which converts any touch-tone phone into an M-F-er."
The tones you hear in touch-tone phones are not the M-F tones that operate the long-distance switching system. Phone phreaks believe AT&T had deliberately equipped touch tones with a different set of frequencies to avoid putting the six master M-F tones in the hands of every touch-tone owner. Ed's complex switching matrix puts the six master tones, in effect puts a blue box, in the hands of every touch-tone owner.
Ed shows me pages of schematics, specifications and parts lists. "It's not easy to build, but everything here is in the HeathKit catalog."
Ed asks Ralph what progress he has made in his attempts to reestablish a long-term open conference line for phone phreaks. The last big conference — the historic "2111" conference — had been arranged through an unused Telex test-board trunk somewhere in the innards of a 4A switching machine in Vancouver, Canada. For months phone phreaks could M-F their way into Vancouver, beep out 604 (the Vancouver area code) and then beep out 2111 (the internal phone-company code for Telex testing), and find themselves at any time, day or night, on an open wire talking with an array of phone phreaks from coast to coast, operators from Bermuda, Tokyo and London who are phone-phreak sympathizers, and miscellaneous guests and technical experts. The conference was a massive exchange of information. Phone phreaks picked each other's brains clean, then developed new ways to pick the phone company's brains clean. Ralph gave “MF boogie” concerts with his home-entertainment-type electric organ, Captain Crunch demonstrated his round-the-world prowess with his notorious computerized unit and dropped leering hints of the "action" he was getting with his girlfriends. (The Captain lives out or pretends to live out several kinds of fantasies to the gossipy delight of the blind phone phreaks who urge him on to further triumphs on behalf of all of them.) The somewhat rowdy Northwest phone-phreak crowd let their bitter internal feud spill over into the peaceable conference line, escalating shortly into guerrilla warfare; Carl the East Coast international tone relations expert demonstrated newly opened direct M-F routes to central offices on the island of Bahrain in the Persian Gulf, introduced a new phone-phreak friend of his in Pretoria, and explained the technical operation of the new Oakland-to-Vietnam linkages. (Many phone phreaks pick up spending money by M-F-ing calls from relatives to Vietnam G.I.'s, charging $5 for a whole hour of trans-Pacific conversation.)
Day and night the conference line was never dead. Blind phone phreaks all over the country, lonely and isolated in homes filled with active sighted brothers and sisters, or trapped with slow and unimaginative blind kids in straitjacket schools for the blind, knew that no matter how late it got they could dial up the conference and find instant electronic communion with two or three other blind kids awake over on the other side of America. Talking together on a phone hookup, the blind phone phreaks say, is not much different from being there together. Physically, there was nothing more than a two-inch-square wafer of titanium inside a vast machine on Vancouver Island. For the blind kids there meant an exhilarating feeling of being in touch, through a kind of skill and magic which was peculiarly their own.
Last April 1, however, the long Vancouver Conference was shut off. The phone phreaks knew it was coming. Vancouver was in the process of converting from a step-by-step system to a 4A machine and the 2111 Telex circuit was to be wiped out in the process. The phone phreaks learned the actual day on which the conference would be erased about a week ahead of time over the phone company's internal-news-and-shop-talk recording.
For the next frantic seven days every phone phreak in America was on and off the 2111 conference twenty-four hours a day. Phone phreaks who were just learning the game or didn't have M-F capability were boosted up to the conference by more experienced phreaks so they could get a glimpse of what it was like before it disappeared. Top phone phreaks searched distant area codes for new conference possibilities without success. Finally in the early morning of April 1, the end came.
"I could feel it coming a couple hours before midnight," Ralph remembers. "You could feel something going on in the lines. Some static began showing up, then some whistling wheezing sound. Then there were breaks. Some people got cut off and called right back in, but after a while some people were finding they were cut off and couldn't get back in at all. It was terrible. I lost it about one a.m., but managed to slip in again and stay on until the thing died... I think it was about four in the morning. There were four of us still hanging on when the conference disappeared into nowhere for good. We all tried to M-F up to it again of course, but we got silent termination. There was nothing there."
The Legendary Mark Bernay Turns Out To Be "The Midnight Skulker"
Mark Bernay. I had come across that name before. It was on Gilbertson's select list of phone phreaks. The California phone phreaks had spoken of a mysterious Mark Bernay as perhaps the first and oldest phone phreak on the West Coast. And in fact almost every phone phreak in the West can trace his origins either directly to Mark Bernay or to a disciple of Mark Bernay.
It seems that five years ago this Mark Bernay (a pseudonym he chose for himself) began traveling up and down the West Coast pasting tiny stickers in phone books all along his way. The stickers read something like "Want to hear an interesting tape recording? Call these numbers." The numbers that followed were toll-free loop-around pairs. When one of the curious called one of the numbers he would hear a tape recording pre-hooked into the loop by Bernay which explained the use of loop-around pairs, gave the numbers of several more, and ended by telling the caller, "At six o'clock tonight this recording will stop and you and your friends can try it out. Have fun."
"I was disappointed by the response at first," Bernay told me, when I finally reached him at one of his many numbers and he had dispensed with the usual "I never do anything illegal" formalities with which experienced phone phreaks open most conversations. "I went all over the coast with these stickers not only on pay phones, but I'd throw them in front of high schools in the middle of the night, I'd leave them unobtrusively in candy stores, scatter them on main streets of small towns. At first hardly anyone bothered to try it out. I would listen in for hours and hours after six o'clock and no one came on. I couldn't figure out why people wouldn't be interested. Finally these two girls in Oregon tried it out and told all their friends and suddenly it began to spread."
Before his Johnny Appleseed trip Bernay had already gathered a sizable group of early pre-blue-box phone phreaks together on loop-arounds in Los Angeles. Bernay does not claim credit for the original discovery of the loop-around numbers. He attributes the discovery to an eighteen-year-old reform-school kid in Long Beach whose name he forgets and who, he says, "just disappeared one day." When Bernay himself discovered loop-arounds independently, from clues in his readings in old issues of the Automatic Electric Technical Journal, he found dozens of the reform-school kid's friends already using them. However, it was one of Bernay's disciples in Seattle who introduced phone phreaking to blind kids. The Seattle kid who learned about loops through Bernay's recording told a blind friend, the blind kid taught the secret to his friends at a winter camp for blind kids in Los Angeles. When the camp session was over these kids took the secret back to towns all over the West. This is how the original blind kids became phone phreaks. For them, for most phone phreaks in general, it was the discovery of the possibilities of loop-arounds which led them on to far more serious and sophisticated phone-phreak methods, and which gave them a medium for sharing their discoveries.
A year later a blind kid who moved back east brought the technique to a blind kids' summer camp in Vermont, which spread it along the East Coast. All from a Mark Bernay sticker.
Bernay, who is nearly thirty years old now, got his start when he was fifteen and his family moved into an L.A. suburb serviced by General Telephone and Electronics equipment. He became fascinated with the differences between Bell and GT&E equipment. He learned he could make interesting things happen by carefully timed clicks with the disengage button. He learned to interpret subtle differences in the array of clicks, whirrs and kachinks he could hear on his lines. He learned he could shift himself around the switching relays of the L.A. area code in a not-too-predictable fashion by interspersing his own hook-switch clicks with the clicks within the line. Independent phone companies — there are nineteen hundred of them still left, most of them tiny island principalities in Ma Bell's vast empire — have always been favorites with phone phreaks, first as learning tools, then as Archimedes platforms from which to manipulate the huge Bell system. A phone phreak in Bell territory will often M-F himself into an independent's switching system, with switching idiosyncrasies that can give him marvelous leverage over the Bell System.
"I have a real affection for Automatic Electric equipment," Bernay told me. "There are a lot of things you can play with. Things break down in interesting ways."
Shortly after Bernay graduated from college (with a double major in chemistry and philosophy), he graduated from phreaking around with GT&E to the Bell System itself, and made his legendary sticker-pasting journey north along the coast, settling finally in Northwest Pacific Bell territory. He discovered that if Bell does not break down as interestingly as GT&E, it nevertheless offers a lot of "things to play with."
Bernay learned to play with blue boxes. He established his own personal switchboard and phone-phreak research laboratory complex. He continued his phone-phreak evangelism with ongoing sticker campaigns. He set up two recording numbers, one with instructions for beginning phone phreaks, the other with latest news and technical developments (along with some advanced instruction) gathered from sources all over the country.
These days, Bernay told me, he had gone beyond phone-phreaking itself. "Lately I've been enjoying playing with computers more than playing with phones. My personal thing in computers is just like with phones, I guess — the kick is in finding out how to beat the system, how to get at things I'm not supposed to know about, how to do things with the system that I'm not supposed to be able to do."
As a matter of fact, Bernay told me, he had just been fired from his computer-programming job for doing things he was not supposed to be able to do. He had been working with a huge time-sharing computer owned by a large corporation but shared by many others. Access to the computer was limited to those programmers and corporations that had been assigned certain passwords. And each password restricted its user to access to only the one section of the computer cordoned off from its own information storager. The password system prevented companies and individuals from stealing each other's information.
"I figured out how to write a program that would let me read everyone else's password," Bernay reports. "I began playing around with passwords. I began letting the people who used the computer know, in subtle ways, that I knew their passwords. I began dropping notes to the computer supervisors with hints that I knew what I know. I signed them 'The Midnight Skulker.' I kept getting cleverer and cleverer with my messages and devising ways of showing them what I could do. I'm sure they couldn't imagine I could do the things I was showing them. But they never responded to me. Every once in a while they'd change the passwords, but I found out how to discover what the new ones were, and I let them know. But they never responded directly to The Midnight Skulker. I even finally designed a program which they could use to prevent my program from finding out what it did. In effect I told them how to wipe me out, The Midnight Skulker. It was a very clever program. I started leaving clues about myself. I wanted them to try and use it and then try to come up with something to get around that and reappear again. But they wouldn't play. I wanted to get caught. I mean I didn't want to get caught personally, but I wanted them to notice me and admit that they noticed me. I wanted them to attempt to respond, maybe in some interesting way."
Finally the computer managers became concerned enough about the threat of information-stealing to respond. However, instead of using The Midnight Skulker's own elegant self-destruct program, they called in their security personnel, interrogated everyone, found an informer to identify Bernay as The Midnight Skulker, and fired him.
"At first the security people advised the company to hire me full-time to search out other flaws and discover other computer freaks. I might have liked that. But I probably would have turned into a double double agent rather than the double agent they wanted. I might have resurrected The Midnight Skulker and tried to catch myself. Who knows? Anyway, the higher-ups turned the whole idea down."
You Can Tap the F.B.I.'s Crime Control Computer in the Comfort of Your Own Home, Perhaps
Computer freaking may be the wave of the future. It suits the phone-phreak sensibility perfectly. Gilbertson, the blue-box inventor and a lifelong phone phreak, has also gone on from phone-phreaking to computer-freaking. Before he got into the blue-box business Gilbertson, who is a highly skilled programmer, devised programs for international currency arbitrage.
But he began playing with computers in earnest when he learned he could use his blue box in tandem with the computer terminal installed in his apartment by the instrumentation firm he worked for. The printout terminal and keyboard were equipped with acoustical coupling, so that by coupling his little ivory Princess phone to the terminal and then coupling his blue box on that, he could M-F his way into other computers with complete anonymity, and without charge; program and re-program them at will; feed them false or misleading information; tap and steal from them. He explained to me that he taps computers by busying out all the lines, then going into a verification trunk, listening into the passwords and instructions one of the time sharers uses, and them M-F-ing in and imitating them. He believes it would not be impossible to creep into the F.B.I's crime control computer through a local police computer terminal and phreak around with the F.B.I.'s memory banks. He claims he has succeeded in re-programming a certain huge institutional computer in such a way that it has cordoned off an entire section of its circuitry for his personal use, and at the same time conceals the arrangement from anyone else's notice. I have been unable to verify this claim.
Like Captain Crunch, like Alexander Graham Bell (pseudonym of a disgruntled-looking East Coast engineer who claims to have invented the black box and now sells black and blue boxes to gamblers and radical heavies), like most phone phreaks, Gilbertson began his career trying to rip off pay phones as a teen-ager. Figure them out, then rip them off. Getting his dime back from the pay phone is the phone phreak's first thrilling rite of passage. After learning the usual eighteen different ways of getting his dime back, Gilbertson learned how to make master keys to coin-phone cash boxes, and get everyone else's dimes back. He stole some phone-company equipment and put together his own home switchboard with it. He learned to make a simple "bread-box" device, of the kind used by bookies in the Thirties (bookie gives a number to his betting clients; the phone with that number is installed in some widow lady's apartment, but is rigged to ring in the bookie's shop across town, cops trace big betting number and find nothing but the widow).
Not long after that afternoon in 1968 when, deep in the stacks of an engineering library, he came across a technical journal with the phone tone frequencies and rushed off to make his first blue box, not long after that Gilbertson abandoned a very promising career in physical chemistry and began selling blue boxes for $1,500 apiece.
"I had to leave physical chemistry. I just ran out of interesting things to learn," he told me one evening. We had been talking in the apartment of the man who served as the link between Gilbertson and the syndicate in arranging the big $300,000 blue-box deal which fell through because of legal trouble. There has been some smoking.
"No more interesting things to learn," he continues. "Physical chemistry turns out to be a sick subject when you take it to its highest level. I don't know. I don't think I could explain to you how it's sick. You have to be there. But you get, I don't know, a false feeling of omnipotence. I suppose it's like phone-phreaking that way. This huge thing is there. This whole system. And there are holes in it and you slip into them like Alice and you're pretending you're doing something you're actually not, or at least it's no longer you that's doing what you thought you were doing. It's all Lewis Carroll. Physical chemistry and phone-phreaking. That's why you have these phone-phreak pseudonyms like The Cheshire Cat, The Red King, and The Snark. But there's something about phone-phreaking that you don't find in physical chemistry." He looks up at me:
"Did you ever steal anything?"
Well yes, I —
"Then you know! You know the rush you get. It's not just knowledge, like physical chemistry. It's forbidden knowledge. You know. You can learn about anything under the sun and be bored to death with it. But the idea that it's illegal. Look: you can be small and mobile and smart and you're ripping off somebody large and powerful and very dangerous."
People like Gilbertson and Alexander Graham Bell are always talking about ripping off the phone company and screwing Ma Bell. But if they were shown a single button and told that by pushing it they could turn the entire circuitry of A.T.&T. into molten puddles, they probably wouldn't push it. The disgruntled-inventor phone phreak needs the phone system the way the lapsed Catholic needs the Church, the way Satan needs a God, the way The Midnight Skulker needed, more than anything else, response.
Later that evening Gilbertson finished telling me how delighted he was at the flood of blue boxes spreading throughout the country, how delighted he was to know that "this time they're really screwed." He suddenly shifted gears.
"Of course, I do have this love/hate thing about Ma Bell. In a way I almost like the phone company. I guess I'd be very sad if they were to go away or if their services were to disintegrate. In a way it's just that after having been so good they turn out to have these things wrong with them. It's those flaws that allow me to get in and mess with them, but I don't know. There's something about it that gets to you and makes you want to get to it, you know."
I ask him what happens when he runs out of interesting, forbidden things to learn about the phone system.
"I don't know, maybe I'd go to work for them for a while."
In security even?
"I'd do it, sure. I just as soon play — I'd just as soon work on either side."
Even figuring out how to trap phone phreaks? I said, recalling Mark Bernay's game.
"Yes, that might be interesting. Yes, I could figure out how to outwit the phone phreaks. Of course if I got too good at it, it might become boring again. Then I'd have to hope the phone phreaks got much better and outsmarted me for a while. That would move the quality of the game up one level. I might even have to help them out, you know, 'Well kids, I wouldn't want this to get around but did you ever think of — ?' I could keep it going at higher and higher levels forever."
The dealer speaks up for the first time. He has been staring at the soft blinking patterns of lights and colors on the translucent tiled wall facing him. (Actually there are no patterns: the color and illumination of every tile is determined by a computerized random-number generator designed by Gilbertson which insures that there can be no meaning to any sequence of events in the tiles.)
"Those are nice games you're talking about," says the dealer to his friend. "But I wouldn't mind seeing them screwed. A telephone isn't private anymore. You can't say anything you really want to say on a telephone or you have to go through that paranoid bull----. 'Is it cool to talk on the phone?' I mean, even if it is cool, if you have to ask 'Is it cool,' then it isn't cool. You know. Like those blind kids, people are going to start putting together their own private telephone companies if they want to really talk. And you know what else. You don't hear silences on the phone anymore. They've got this time-sharing thing on long-distance lines where you make a pause and they snip out that piece of time and use it to carry part of somebody else's conversation. Instead of a pause, where somebody's maybe breathing or sighing, you get this blank hole and you only start hearing again when someone says a word and even the beginning of the word is clipped off. Silences don't count — you're paying for them, but they take them away from you. It's not cool to talk [i.e., if you’re paranoid about being tapped], and you can't hear someone when they don't talk. What the hell good is the phone? I wouldn't mind seeing them totally screwed."
The Big Memphis Bust
Joe Engressia never wanted to screw Ma Bell. His dream had always been to work for her.
The day I visited Joe in his small apartment on Union Avenue in Memphis, he was upset about another setback in his application for a telephone job.
"They're stalling on it. I got a letter today telling me they'd have to postpone the interview I requested again. My landlord read it for me. They gave me some runaround about wanting papers on my rehabilitation status but I think there's something else going on."
When I switched on the forty-watt bulb in Joe's room — he sometimes forgets when he has guests — it looked as if there was enough telephone hardware to start a small phone company of his own.
There is one phone on top of his desk, one phone sitting in an open drawer beneath the desk top. Next to the desk-top phone is a cigar-box-size M-F device with big toggle switches, and next to that is some kind of switching and coupling device with jacks and alligator plugs hanging loose. Next to that is a Braille typewriter. On the floor next to the desk, lying upside down like a dead tortoise, is the half-gutted body of an old black standard phone. Across the room on a torn and dusty couch are two more phones, one of them a touch-tone model; two tape recorders; a heap of phone patches and cassettes, and a life-size toy telephone.
Our conversation is interrupted every ten minutes by phone phreaks from all over the country ringing Joe on just about every piece of equipment but the toy phone and the Braille typewriter. One fourteen-year-old blind kid from Connecticut calls up and tells Joe he's got a girl friend. He wants to talk to Joe about girlfriends. Joe says they'll talk later in the evening when they can be alone on the line. Joe draws a deep breath, whistles him off the air with an earsplitting 2600-cycle whistle. Joe is pleased to get the calls but he looked worried and preoccupied that evening, his brow constantly furrowed over his dark wandering eyes. In addition to the phone-company stall, he has just learned that his apartment house is due to be demolished in sixty days for urban renewal. For all its shabbiness, the Union Avenue apartment house has been Joe's first home-of-his-own and he's worried that he may not find another before this one is demolished.
But what really bothers Joe is that switchmen haven't been listening to him. "I've been doing some checking on 800 numbers lately, and I've discovered that certain 800 numbers in New Hampshire couldn't be reached from Missouri and Kansas. Now it may sound like a small thing, but I don't like to see sloppy work; it makes me feel bad about the lines. So I've been calling up switching offices and reporting it, but they haven't corrected it. I called them up for the third time today and instead of checking they just got mad. Well, that gets me mad. I mean, I do try to help them. There's something about them I can't understand — you want to help them and they just try to say you're defrauding them."
It is Sunday evening and Joe invites me to join him for dinner at a Holiday Inn. Frequently on Sunday evening Joe takes some of his welfare money, calls a cab, and treats himself to a steak dinner at one of Memphis' thirteen Holiday Inns. Memphis is the headquarters of Holiday Inn. Holiday Inns have been a favorite for Joe ever since he made his first solo phone trip to a Bell switching office in Jacksonville, Florida, and stayed in the Holiday Inn there. He likes to stay at Holiday Inns, he explains, because they represent freedom to him and because the rooms are arranged the same all over the country so he knows that any Holiday Inn room is familiar territory to him. Just like any telephone.
Over steaks in the Pinnacle Restaurant of the Holiday Inn Medical Center on Madison Avenue in Memphis, Joe tells me the highlights of his life as a phone phreak.
At age seven, Joe learned his first phone trick. A mean baby-sitter, tired of listening to little Joe play with the phone as he always did, constantly, put a lock on the phone dial. "I got so mad. When there's a phone sitting there and I can't use it . . . so I started getting mad and banging the receiver up and down. I noticed I banged it once and it dialed one. Well, then I tried banging it twice. . . ." In a few minutes Joe learned how to dial by pressing the hook switch at the right time. "I was so excited I remember going 'whoo whoo' and beat a box down on the floor."
At age eight Joe learned about whistling. "I was listening to some intercept nonworking-number recording in L.A. — I was calling L.A. as far back as that, but I'd mainly dial nonworking numbers because there was no charge, and I'd listen to these recordings all day. Well, I was whistling 'cause listening to these recordings can be boring after a while even if they are from L.A., and all of a sudden, in the middle of whistling, the recording clicked off. I fiddled around whistling some more, and the same thing happened. So I called up the switch room and said, 'I'm Joe. I'm eight years old and I want to know why when I whistle this tune the line clicks off.' He tried to explain it to me, but it was a little too technical at the time. I went on learning. That was a thing nobody was going to stop me from doing. The phones were my life, and I was going to pay any price to keep on learning. I knew I could go to jail. But I had to do what I had to do to keep on learning."
The phone is ringing when we walk back into Joe's apartment on Union Avenue. It is Captain Crunch. The Captain has been following me around by phone, calling up everywhere I go with additional bits of advice and explanation for me and whatever phone phreak I happen to be visiting. This time the Captain reports he is calling from what he describes as "my hideaway high up in the Sierra Nevada." He pulses out lusty salvos of M-F and tells Joe he is about to "go out and get a little action tonight. Do some phreaking of another kind, if you know what I mean." Joe chuckles.
The Captain then tells me to make sure I understand that what he told me about tying up the nation's phone lines was true, but that he and the phone phreaks he knew never used the technique for sabotage. They only learned the technique to help the phone company.
"We do a lot of troubleshooting for them. Like this New Hampshire/Missouri WATS-line flaw I've been screaming about. We help them more than they know."
After we say good-bye to the Captain and Joe whistles him off the line, Joe tells me about a disturbing dream he had the night before: "I had been caught and they were taking me to a prison. It was a long trip. They were taking me to a prison a long long way away. And we stopped at a Holiday Inn and it was my last night ever at a Holiday Inn, and it was my last night ever using the phone and I was crying and crying, and the lady at the Holiday Inn said, 'Gosh, honey, you should never be sad at a Holiday Inn. You should always be happy here. Especially since it's your last night.' And that just made it worse and I was sobbing so much I couldn't stand it."
Two weeks after I left Joe Engressia's apartment, phone-company security agents and Memphis police broke into it. Armed with a warrant, which they left pinned to a wall, they confiscated every piece of equipment in the room, including his toy telephone. Joe was placed under arrest and taken to the city jail where he was forced to spend the night since he had no money and knew no one in Memphis to call.
It is not clear who told Joe what that night, but someone told him that the phone company had an open-and-shut case against him because of revelations of illegal activity he had made to a phone-company undercover agent.
By morning Joe had become convinced that the reporter from Esquire, with whom he had spoken two weeks ago, was the undercover agent. He probably had ugly thoughts about someone he couldn't see gaining his confidence, listening to him talk about his personal obsessions and dreams, while planning all the while to lock him up.
"I really thought he was a reporter," Engressia told the Memphis Press-Scimitar. "I told him everything...." Feeling betrayed, Joe proceeded to confess everything to the press and police.
As it turns out, the phone company did use an undercover agent to trap Joe, although it was not the Esquire reporter.
Ironically, security agents were alerted and began to compile a case against Joe because of one of his acts of love for the system: Joe had called an internal service department to report that he had located a group of defective long-distance trunks, and to complain again about the New Hampshire/Missouri WATS problem. Joe always liked Ma Bell's lines to be clean and responsive. A suspicious switchman reported Joe to the security agents who discovered that Joe had never had a long-distance call charged to his name.
Then the security agents learned that Joe was planning one of his phone trips to a local switching office. The security people planted one of their agents in the switching office. He posed as a student switchman and followed Joe around on a tour. He was extremely friendly and helpful to Joe, leading him around the office by the arm. When the tour was over he offered Joe a ride back to his apartment house. On the way he asked Joe — one tech man to another — about "those blue boxes" he'd heard about. Joe talked about them freely, talked about his blue box freely, and about all the other things he could do with the phones.
The next day the phone-company security agents slapped a monitoring tap on Joe's line, which eventually picked up an illegal call. Then they applied for the search warrant and broke in.
In court Joe pleaded not guilty to possession of a blue box and theft of service. A sympathetic judge reduced the charges to malicious mischief and found him guilty on that count, sentenced him to two thirty-day sentences to be served concurrently and then suspended the sentence on condition that Joe promise never to play with phones again. Joe promised, but the phone company refused to restore his service. For two weeks after the trial Joe could not be reached except through the pay phone at his apartment house, and the landlord screened all calls for him.
Phone phreak Carl managed to get through to Joe after the trial, and reported that Joe sounded crushed by the whole affair.
"What I'm worried about," Carl told me, "is that Joe means it this time. The promise. That he'll never phone-phreak again. That's what he told me, that he's given up phone-phreaking for good. I mean his entire life. He says he knows they're going to be watching him so closely for the rest of his life he'll never be able to make a move without going straight to jail. He sounded very broken up by the whole experience of being in jail. It was awful to hear him talk that way. I don't know. I hope maybe he had to sound that way. Over the phone, you know."
Video: Steve Wozniak Remembers Steve Jobs
He reports that the entire phone-phreak underground is up in arms over the phone company's treatment of Joe. "All the while Joe had his hopes pinned on his application for a phone-company job, they were stringing him along getting ready to bust him. That gets me mad. Joe spent most of his time helping them out. The bastards. They think they can use him as an example. All of sudden they're harassing us on the coast. Agents are jumping up on our lines. They just busted ------'s mute yesterday and ripped out his lines. But no matter what Joe does, I don't think we're going to take this lying down."
Two weeks later my phone rings and about eight phone phreaks in succession say hello from about eight different places in the country, among them Carl, Ed, and Captain Crunch. A nationwide phone-phreak conference line has been reestablished through a switching machine in --------, with the cooperation of a disgruntled switchman.
"We have a special guest with us today," Carl tells me.
The next voice I hear is Joe's. He reports happily that he has just moved to a place called Millington, Tennessee, fifteen miles outside of Memphis, where he has been hired as a telephone-set repairman by a small independent phone company. Someday he hopes to be an equipment troubleshooter.
"It's the kind of job I dreamed about. They found out about me from the publicity surrounding the trial. Maybe Ma Bell did me a favor busting me. I'll have telephones in my hands all day long.”
