A Printer That Sings Your Data for Hackers to Hear
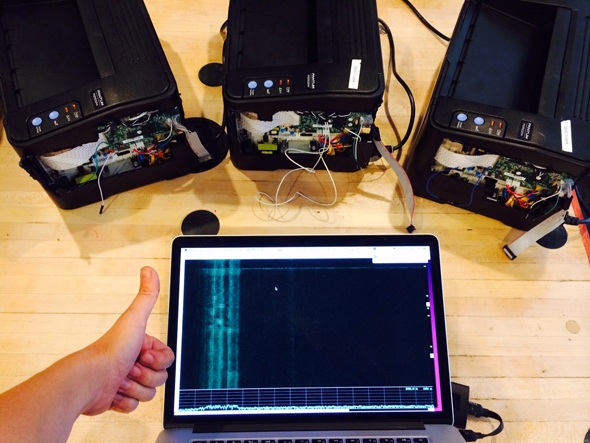
Photo from Ang Cui
Like dial-up modems, our printers sing us familiar songs. We get used to the whine of their paper feeders, rollers, and gears, and it’s reassuring to hear the same percussive melody every time something prints. It means everything is working normally. But last week I heard a melodious printer song that meant something was very wrong. The printer had been hacked.
At the Black Hat cybersecurity conference Wednesday, researcher Ang Cui is presenting this “Funtenna” project, which is a proof of concept that an attacker who has compromised an embedded device like a printer can manipulate its hardware through software alone to transmit data over audible sound waves or even the radio spectrum.
An increasingly large body of research shows how easy it is to compromise Internet of Things devices. And Funtenna builds on this by looking at one thing a hacker could do next once she inconspicuously took control of an embedded device. Using only software commands, Cui shows that an attacker could turn the integrated circuit pins and other electromechanical components in a cheap network printer (under $50) into transmitters, sending data to the attacker’s off-site receiver.
The idea is to find a method for pilfering data that won’t be detected by network-monitoring software. Cui, who runs a company that makes security software for Internet of Things devices (which are notoriously underprotected), is always trying to get in the mind of an attacker whose goal is compromising the computers inside everyday objects. Cui noticed that some observations and experiments talked about using hardware in embedded devices to transmit data (not to mention NSA programs), but they didn't directly discuss what was possible, so he started working on Funtenna in his free time.
“Traditional network intrusion detection systems all basically focus on looking at every packet and understanding what’s good and what’s bad,” Cui said. (Packets are data transmitted over a network.) “But now we’re changing the game. The packets are here in an AM radio so good luck storing that packet and figuring it out.” Instead of trying to get bank account, credit card, or social security numbers (or any other valuable data) off a network using traditional digital modes like email, a hacker could use Funtenna methods to transmit the data to herself through channels that aren’t monitored as part of traditional network security.
There are multiple Funtenna demos for both audio frequencies and the electromagnetic spectrum. Cui can make the printer sing its own boot-up code, send out ultrasonic broadcasts, transmit to a dinky handheld AM radio receiver (or a more powerful antenna), and even make slow and low vibrations that are only detectible by a sensor called a geophone. And where did Cui get a geophone? “It’s ghost-hunting equipment I got from Amazon. It’s meant to hear the footsteps of ghosts.” Yes.
Many of the demos show techniques that would be impractical for an actual covert operation. If printers all over a large office were singing out sensitive data, someone would eventually realize that something was wrong with the devices (even if they didn’t know what) and shut them down. Likewise, transmitting data through very slow vibrations is inefficient, and it’s hard to distinguish them from other low tremors from far away. For example, elephants can detect one another’s stomps when they are miles apart, but they probably couldn’t do it in an urban area. “These are intuitive demonstrations of what’s possible,” Cui said.
In the radiofrequency demo, one way to boost the signal strength would be to coordinate multiple devices on a network to all transmit the same things at the same time. “This has a hope of going at least out of this room, and if you had enough of these things going at the same time, it probably has a good chance of getting out of the building,” he said. “We could run exactly the same code on a phone and a printer at the same time and you should expect to see the same kind of data. So this is not something we can just do on the printer, we can do it pretty much for all the IoT things you see around.”
Still, proof of concept is the key phrase, because Cui’s techniques are currently very limited. Things like interference from AV equipment or receiver positioning can throw off the results. But the goal is primarily to show the technique’s potential. “This idea of using software to actively emanate signals out can’t possibly be a new idea,” he said. “But it’s not talked about very much in the clear.”
Future Tense is a partnership of Slate, New America, and Arizona State University.
