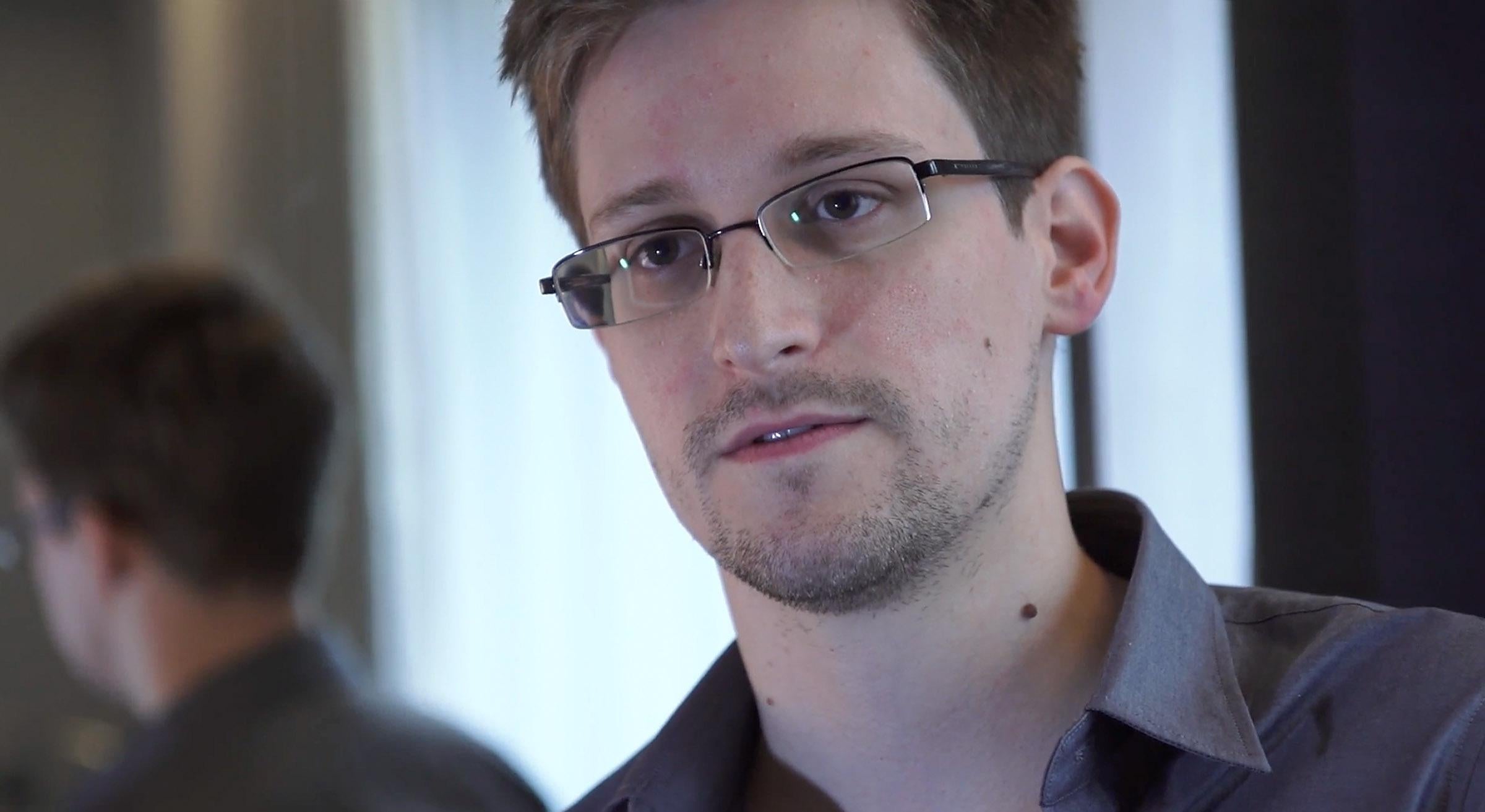
One of the only ways to shield against government surveillance is to use encryption tools to communicate securely. But the National Security Agency has made significant progress cracking popular encryption protocols in recent years, according to secret documents leaked by former NSA contractor Edward Snowden.
The New York Times, ProPublica, and the Guardian jointly reported Thursday that the NSA has been investing millions in its attempts to gain access to enciphered data sent over the Internet. According to the reports, the NSA made a significant breakthrough in 2010, enabling it to monitor “large amounts” of data flowing through the world’s fiber-optic cables by cracking encryption. As suggested in previously leaked documents about the X-KEYSCORE Internet surveillance system, the NSA and its British counterpart GCHQ have in some cases gained access to data sent over virtual private networks, which are commonly used by businesses and privacy-conscious Internet users to encrypt browsing traffic and conceal IP addresses. And the agency has also worked to deliberately insert vulnerabilities into some international security standards, in an apparent attempt to undermine encryption to make it easier to break.
However, many crucial questions about the scope of the NSA’s decryption capabilities remain unanswered. The latest Snowden scoops adopt an alarmist tone, presenting what is essentially an apocalyptic vision of a world in which encryption has been rendered all but useless because of NSA supercomputers. But it seems clear from the reports that the NSA is still often forced to rely on vulnerabilities to hack into targets’ computers to bypass encryption. In some cases, in order to unscramble information, the agency also has to find ways to obtain the private “keys” used to decrypt it.*
The Guardian report says that the NSA has “capabilities” that can be used to crack Internet traffic encrypted using SSL, which shows up in the browser as HTTPS (unlike unencrypted HTTP). But it has long been known that ”capabilities” to get at SSL traffic exist, with governments and criminal hackers able to perform so-called “man-in-the-middle” attacks to covertly impersonate security certificates and secretly intercept data. Alternatively, the U.S. government may have coerced some companies into handing over their private SSL keys, or could even have obtained the keys through hacking. Either way, it seems highly unlikely that the NSA has worked out how to instantly decrypt SSL traffic indiscriminately and en masse as it is flowing across the cables that make up the Internet’s backbone. (If it had, there would be no need for the PRISM program, which involves the NSA using secret court orders to obtain data from Internet companies such as Google, Apple, and Yahoo.)
Undoubtedly, the NSA’s ceaseless aggressive efforts to crack encryption degrade the overarching security of the Internet’s infrastructure over time. But Snowden himself said in an interview in June that “encryption works” if implemented properly. PGP—used to strongly encrypt email and other data—is still likely to cause the NSA, GCHQ, and other spy agencies serious difficulties, and the same can be said about “off the record” instant messaging, and other peer-to-peer encrypted communications tools, such as Jitsi, Redphone, Silent Circle, and TextSecure. If the NSA can’t crack the encryption a target is using, it can certainly still use a spy Trojan to infiltrate a computer or smartphone and bypass the encryption. However, that the NSA is almost certainly forced in some cases to adopt hacking tactics to grab communications before they are encrypted illustrates that encryption per se is not fundamentally broken and can still help shield against dragnet government surveillance. At least, for now.
*Update, Sept. 6, 2013: This blog post originally stated that the NSA sometimes has to find private keys that were used to encrypt information. However, in public-key cryptography private keys are used to decrypt information that has already been encrypted.