If you have ever searched the Internet for something the NSA has deemed “suspicious,” you may have found yourself flagged up on the screen of a government spy. At least, that’s what a series of newly published secret documents suggest—raising fresh privacy concerns about the pervasive reach of the NSA’s global surveillance programs.
On Wednesday, the Guardian disclosed a range of new details about an NSA program called “XKEYSCORE,” which is an international system used by the NSA to secretly siphon data directly off of Internet networks. A small amount of information was first revealed about this system earlier this month by Brazilian newspaper O Globo, which published secret documents that appeared to show how the NSA was able to use XKEYSCORE to spy on Google maps searches.
The new release compounds the earlier disclosures, revealing how the NSA can use XKEYSCORE to collect and monitor huge troves of data on unencrypted Internet browsing sessions in countries across the world. In one 30-day period in 2012, at least 41 billion total records were collected and stored in XKEYSCORE, according to the Guardian. The NSA claims to have more than 700 XKEYSCORE servers located around the world at approximately 150 sites. At some of these locations the NSA claims it gobbles up more than 20 terabytes of data every day—the equivalent of about 20,000 copies of the Encyclopaedia Britannica. Metadata collected by the system is typically retained, according to the slides, for 30 days at a time. It also appears to be able to sift through the content of unencrypted communications sent over the Internet.
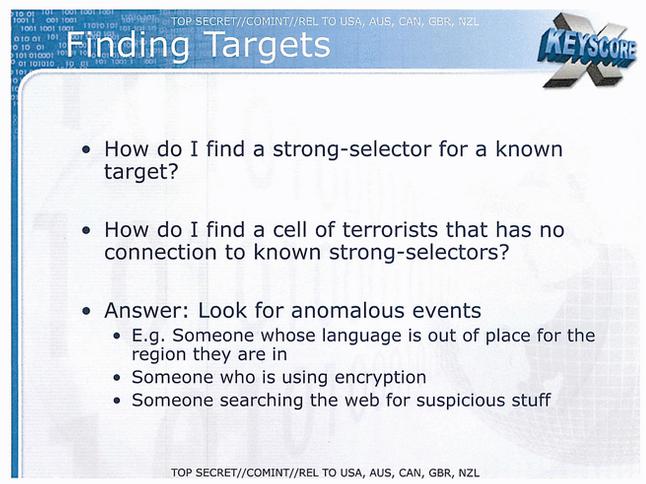
Particularly notable is a series of secret NSA slides on the program, dated from 2008. The slides are marked “release to” United Kingdom, New Zealand, Australia, and Canada, suggesting XKEYSCORE is accessible to spy agencies in each of these countries. (It is also reportedly used by German authorities.) They show how the NSA collects data on emails, browsing sessions, and what people are searching for online—“nearly everything a typical user does on the internet,” as one slide puts it. The system enables analysts to trawl through this information in order to find what is described in the slides as “anomalous events.” Anyone sending encrypted emails or documents, searching for things deemed “suspicious stuff,” or using a language that is “out of place” for the region they are in may get flagged up as a potential target for further surveillance.
However, the increasing adoption of encryption in recent years may have to some degree thwarted the scope of XKEYSCORE’s capabilities. Back in 2008, the NSA could certainly use the XKEYSCORE program to mine vast quantities of data directly from networks about Google searches, email correspondence, and Facebook chats. But since 2008, these websites have broadened their implementation of SSL encryption—which displays in the browser as HTTPS as opposed to unencrypted HTTP—meaning that users’ Internet sessions are more secure and harder to eavesdrop on. Google searches are now automatically encrypted when you are logged into a Google account, for instance, and if you are not logged in you can direct your browser to https://encrypted.google.com. Between 2010 and 2011, Facebook gave users the ability to turn on HTTPS and it was activated by default for Gmail and Twitter users. (Incidentally, you can ensure that you are browsing as much of the Internet as possible using an encrypted connection by installing an add-on called HTTPS Everywhere.)
But encryption is not flawless, and the newly disclosed XKEYSCORE slides seem to illustrate that, too. The 2008 slides suggest that the NSA is able to decrypt data on people who have turned to a Virtual Private Network in order to anonymize their Internet use by masking their IP address. The NSA claims it can “discover the users” of VPNs, suggesting, again, that people using encryption or anonymizing tools may find themselves targeted as suspicious merely for attempting to protect the privacy of their communications. Separately, the U.S. government has been attempting to pressure Internet companies to hand over the keys that would allow it to snoop on encrypted SSL traffic, CNET recently reported.
Either way, using encryption remains the only real option you have when it comes to securing your communications on the Web from systems like XKEYSCORE. Edward Snowden, the NSA contractor who leaked the documents on the surveillance programs, has stated that “encryption works”—and the more people adopt encryption tools, the less likely their use will be deemed suspicious.