In time, we may look back on Russia’s interference with the 2016 presidential election as the good old days of cybercrime and information warfare. Sure, poorly protected computers enabled some fairly dramatic attempts at large-scale manipulation and humiliation—but on the bright side, there was nothing subtle or secret about it. Large-scale dumps of embarrassing political documents on Wikileaks are far preferable to the activity that Bloomberg attributed to Russian hackers this week: demanding payments from liberal U.S. organizations to prevent their stolen data from being released.
According to Bloomberg reporter Michael Riley, at least a dozen progressive groups have been told to make payments ranging from $30,000 to $150,000 or face the public release of compromising stolen emails and files. It’s not yet clear whether the Russian government is actually driving these extortion efforts, and the sums of money demanded in anonymous Bitcoin payments seem far too small to be of much interest to a major national government. But, Riley writes, the perpetrators of these extortion attempts “used some of the techniques that security experts consider hallmarks of Cozy Bear,” the Russian government hacking group.
Whether or not a foreign government is making these particular ransom demands, they’re an important reminder that governments certainly could leverage their ability to compromise computer networks as a tool for demanding money or other concessions from U.S political organizations. Wikileaks dumps are a fairly crude, blunt instrument for manipulation. Targeted blackmail has the potential to be a much defter and more dangerous one.
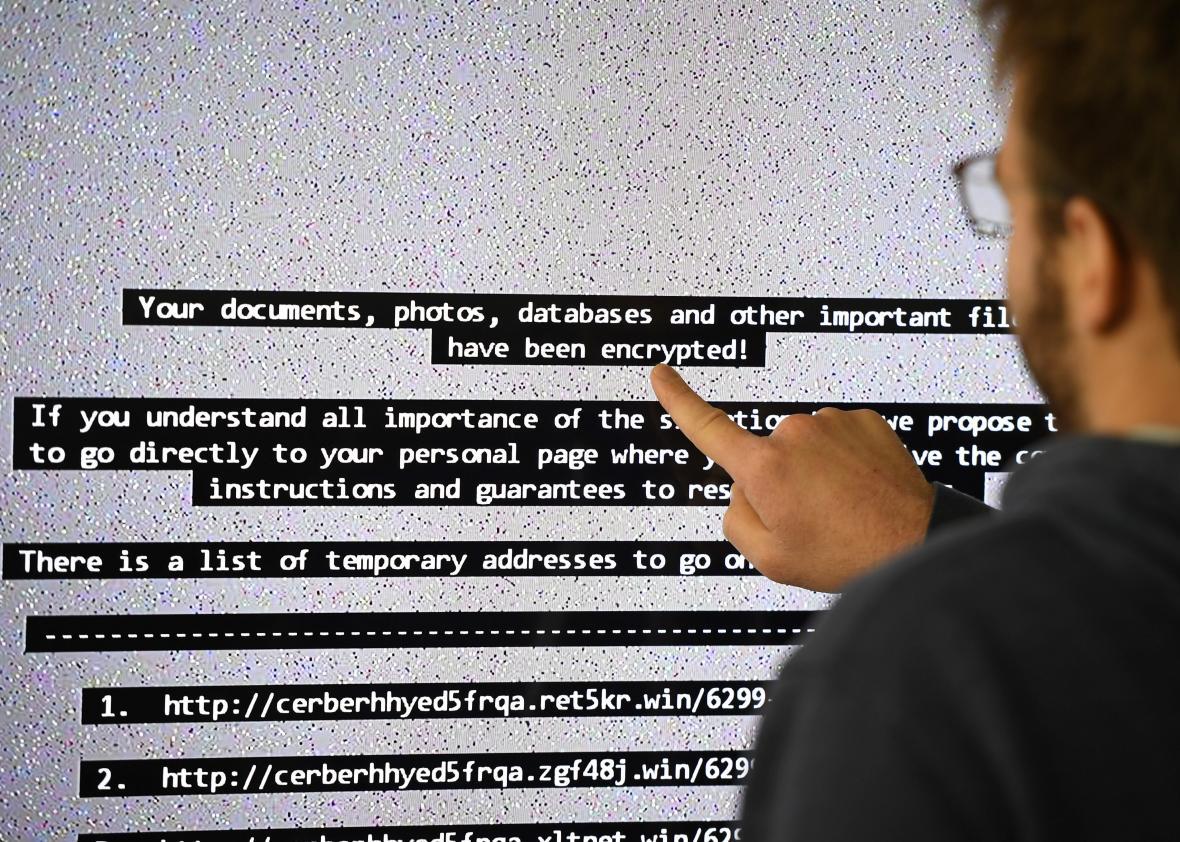
Online extortion is not new—ransomware has been plaguing victims for years, enabled by the development of anonymous, largely untraceable cryptocurrencies like Bitcoin—and it undoubtedly has a bright criminal future. Extortion eliminates the need for cyber thieves to find customers for their stolen data or risk wading into black market forums where law enforcement officials may be lurking. It allows criminals to wring value out of even the least interesting or commercially valuable information by selling it back to the one person to whom it has value: you.
Furthermore, we’re hurtling toward a future of more and more Internet-connected devices that will perform crucial everyday functions but store very little interesting data. In this world, extortion will give criminals a way to profit off compromising your light bulbs or refrigerator or toaster oven. There’s unlikely to be data of any value to you (or anyone else) stored on those devices, but you’d probably be willing to pay a small ransom to someone who figured out how to make them malfunction in sufficiently irritating ways.
But you shouldn’t. And the groups currently being targeted shouldn’t pay up, either, even if the release of profoundly humiliating—or even compromising—information is at stake. There may be a small number of special, life-threatening circumstances in which paying an online ransom demand is the right choice—at a hospital, for instance, or stuck inside a compromised moving vehicle. But otherwise, it is absolutely the worst thing victims can do both for themselves and for everyone else.
That may seem sort of counterintuitive—obviously there are some kinds of public humiliation that it could be worth $30,000 to avoid. To some organizations, it may even seem easier (and perhaps cheaper, too) to pay off online intruders than to invest in better protections for their computer systems. But an organization that agrees to pay the hush money has no guarantees that the information won’t still end up being released—or, even more likely, that their adversary won’t return a few months later to demand an additional payment. Unlike a kidnapping victim who can be safely returned, or even a hard drive encrypted by ransomware that can be decrypted upon payment, someone who has stolen your data will likely always retain a copy of that data. That means no amount of paid ransom will ever definitively resolve the situation to the victim’s satisfaction.
Paying ransoms and caving to extortion demands just encourages more of the same activity, directed at both previous victims and new ones. The only way to effectively discourage this kind of crime is to make it so fruitless, so unprofitable, so profoundly ineffective that the perpetrators find a new outlet for their energies. And the only way to do that is to stop relying on individual victims and organizations to make these choices themselves and implement policies that explicitly penalize the payment of online ransoms in most circumstances.
Comparable policies outlawing the payment of ransoms for kidnapping victims—and freezing the assets of their families to prevent such payments—have, unsurprisingly, been very controversial. A 2013 study of the 1991 Italian law that froze kidnapping victims’ families’ assets found that the policy ultimately reduced the number of kidnappings in Sardinia as well as the duration of such incidents. Others have argued pretty persuasively that, in the case of kidnapping, when victims’ lives are at stake, an outright ban may be too stringent a policy, leading to deaths that might otherwise have been avoided.
These arguments lose much of their force when transferred to the realm of online extortion where, for now at least, few lives hang in the balance and all hope of tracking the perpetrators by following the payment pretty much disappears given the nature of cryptocurrencies. Most of these payments, including the ones demanded of breached liberal groups, should be illegal—or, at the very least, heavily taxed.
That may seem like an unfair burden to put on the victims of these crimes when it’s the perpetrators who are at fault and deserve to be punished. But as is so often the case when it comes to online crime, identifying the perpetrators is difficult—and even if they can be identified, there’s no guarantee they’ll fall within the jurisdiction of U.S. laws. So the onus has to fall on the rest of us, even if it means sometimes sacrificing our pride, our data, and our reputations when we might have much preferred to just spend a little money.