Digitially connecting cars to each other and to highway infrastructure promises to drastically reduce collisions and traffic jams. But that wireless vehicular chatter comes at a cost to your privacy: A car that never shuts up may be a lot easier to track.
Researchers at the Universities of Twente in the Netherlands and Ulm in Germany have found that they can use just a few thousands of dollars’ worth of equipment to track a vehicle that’s emitting the so-called “connected vehicle” wireless communications proposed for future vehicle-to-vehicle connections.
With only two $550 devices strategically planted at intersections on the University of Twente’s 432-acre campus, they were able to follow unique signatures in cars’ radio communications, predicting which of two campus regions the vehicle was in with 78 percent accuracy, as well as the car’s more precise location on a specific road with 40 percent accuracy. Extrapolating from that proof-of-concept, the researchers believe that the same technique, expanded with a few hundred thousand dollars of hardware, could be used by governments or even amateurs to monitor vehicles over an entire small city.
“The vehicle is saying ‘I’m Alice, this is my location, this is my speed and my direction.’ Everyone around you can listen to that,” says Jonathan Petit, one of the authors of the study, which will be presented at the Black Hat Europe security conference next month and was first reported by IEEE Spectrum. “They can say, ‘there’s Alice, she claimed she was at home, but she drove by the drug store, went to a fertility clinic,” this kind of thing … Someone can infer a lot of private information about the passenger.”
The proposed connected car protocol, which the National Highway Traffic and Safety Administration (NHTSA) will consider mandating for the first time in American cars in 2017, uses the Wi-Fi-like 802.11p wireless signal and could allow cars to communicate with both each other and with highway infrastructure like roads or bridges. One NHTSA study in 2010 estimated that the protocol could prevent as many as 81 percent of all vehicle collisions.
But Petit, one of the University of Twente researchers, says that with the range of that wireless communication falling between roughly 300 and 900 feet, it could also serve as a powerful surveillance mechanism. It’s not yet clear how often connected vehicles will vary the unique wireless signatures that identify them, which could limit their use for tracking an individual car. But depending on how long those “pseudonyms” remain constant, Petit argues the connected vehicle protocol could offer a new, relatively cheap form of vehicle tracking that could bolster existing law enforcement tracking techniques like automatic license plate readers. Or, he imagines, hackers could collect and crowdsource data from the system to assemble a database of vehicle movements around entire cities.
“When you do a deployment like this, you need to think about privacy,” says Petit. “It was clear that we needed to perform this attack, to demonstrate that this information is accessible to anyone.”
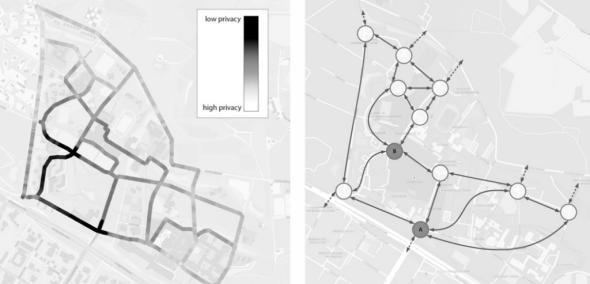
For their proof-of-concept, the researchers used two Cohda Wireless MK3 radio modules and attached a pair of Smarteq antennae to each one, at a total cost of about $1,100 dollars. With those modules located at two intersections on the Twente campus, they could roughly track a vehicle that contained an active Nexcom 802.11p radio beacon. The graphs below show the location of the intersections where those two modules were planted and a “privacy heat map” of how accurately the researchers could predict a car’s location based on the resulting radio readings.
Wired
Though their two modules only gave them about a 40 percent chance of locating the vehicle at any given time down to a 65 foot area, the researchers extrapolated that a few more modules could give them much more precision. Each added radio module at an intersection offers more information about where a target car has been spotted and which direction it’s turned at a given time. If the researchers were to cover eight of the campus’ 21 intersections (at a cost of $4,400 dollars), for instance, they believe they could predict the location of the target vehicle with 90 percent accuracy.
In their paper, the researchers calculate that they could extend that surveillance to an entire city for less than half a million dollars. They write that the system could cover the nearby Dutch city of Enschede, for instance, with more than 150,000 people and 35,200 acres of land, for around $362,000. And they believe that their “sniffing stations” could easily drop in price—they even speculate that one could likely soon be built for a tenth of the cost using a Raspberry Pi minicomputer—to vastly cut the cost of that tracking. “If you have sufficient coverage of a city, you can track everyone,” Petit says.
Programming vehicles to switch their unique radio signatures more often could alleviate some of those privacy concerns, Petit notes. And Petit acknowledges that industry groups like the Crash Avoidance Metrics Partnership in the US and the Car-2-Car Consortium in Europe are considering that privacy fix. (Neither organization immediately responded to Wired’s request for comment.)
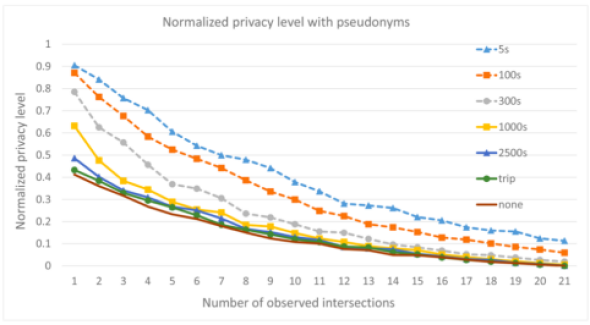
But Petit says more study is needed to understand exactly how much those pseudonym protections can foil tracking. With a high enough density of tracking modules, the researchers caution that someone could overcome even rapid pseudonym-switching to pervasively follow vehicles’ whereabouts. The chart below shows how often the researchers calculate that they could predict the location of a vehicle given different numbers of tracking modules and different lengths of time between vehicle pseudonym changes. (A “privacy score” of 1 means no chance of a vehicle being identified, and a zero means 100 percent certainty of identifying it.)
Wired
Even so, Petit argues that graph should still be evidence that the pseudonym-switching strategy needs to be built into car-to-car communication systems. Though rapidly changing the vehicle’s signature can’t combat some sort of “global observer,” he says, it can still block cheaper, lower resource types of surveillance.
“Pseudonym changing doesn’t stop tracking. It can only mitigate this attack,” says Petit. “But it’s still needed to improve privacy against this mid-size observer…We want to demonstrate that in any deployment, you still have to have this protection, or someone will be able to track you.”
Also in Wired:
IBM Is About to Become the Best Weather Forecaster Ever
Edward Snowden May Be the Most Powerful Person on Twitter
Teen Who Hacked CIA Director’s Email Tells How He Did It
