Spying on bank accounts is most commonly associated with criminals, not nation states. But that could be about to change.
Today, security experts at Kaspersky Lab revealed their discovery of a new “banking Trojan” named Gauss. According to Kaspersky’s researchers, Gauss is related to the Flame surveillance tool described in May as “one of the most complex threats ever discovered.” The Washington Post reported in June that Flame had been jointly developed by the United States and Israel to secretly map and monitor Iran’s computer networks as part of a cyberwarfare campaign.
Based on the same platform as Flame and sharing some of its functionalities, Gauss can harvest data from computers and send the mined information back to the attackers. Kaspersky’s analysts found that it could hijack account information for social network, email, and IM accounts; intercept browser cookies and passwords; infect USB sticks with a data stealing module; list the content of the system drives and folders; and steal credentials for various banking systems in the Middle East.
Kaspersky estimates that it could have targeted “tens of thousands of victims,” and the researchers say that since late May 2012 they have recorded more than 2,500 infections. The highest number of infections were found in Lebanon, followed by Israel, and Palestine. A smaller number of cases were also detected in the United States, the United Arab Emirates, Qatar, Jordan, Germany, and Egypt.
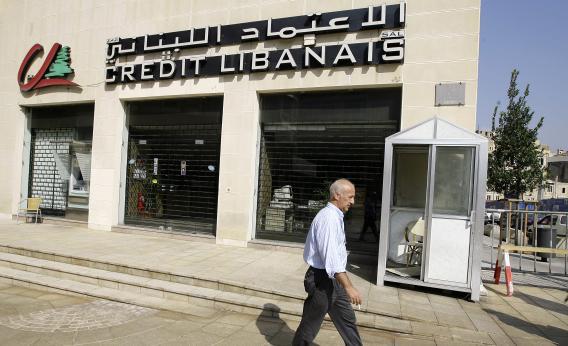
Most controversially, Kaspersky noted that Gauss used Mozilla Firefox-compatible browser plug-ins “designed to steal and monitor data from the clients of several Lebanese banks” including the Bank of Beirut, EBLF, BlomBank, ByblosBank, FransaBank and Credit Libanais. In addition, it targets users of New York-based Citibank and popular Internet service PayPal. But unlike other banking Trojans, “it appears to have been fine-tuned, in the sense that it doesn’t target hundreds of financial institutions, but a select list of online banking institutions.”
In June, the New York Times revealed that President Obama had secretly ordered sophisticated attacks on Iran, expanding a cyberweapons program that had begun under George W. Bush and which had led to the development of Stuxnet in partnership with Israel. The question is now whether Gauss was part of that same nation-state backed initiative, which appears to be increasingly far-reaching and legally dubious. The researchers at Kaspersky are in little doubt as to who were responsible. “We have evidence that Gauss was created by the same ‘factory’ (or factories) that produced Stuxnet, Duqu and Flame,” they say.