This week you may have heard about something called Shellshock. It’s a vulnerability in something else called Bash. Oh, and Bash is a Unix shell. And the Shellshock vulnerability may be larger than Heartbleed—the bug in a widely used open-source encryption library that was revealed earlier this year. What the heck is going on? Let’s talk it out.
First of all, Unix is an operating system that appears in a lot of different forms. Apple’s OS X operating systems, for example, are Unix-based, but Unix is also widely used in servers and other networked devices like modems or security cameras. You run into it much more often than you think.
A Unix shell is your window into how the operating system is actually running. Instead of the graphical user interface (the thing we are usually interacting with on our personal computers), you type text directions into what’s called a command line, and instruct the computer to execute tasks. And you’re usually using a Unix shell like Bash through what’s called a terminal emulator. That’s why the command line program in Apple’s OS X operating systems is called Terminal.
OK, now let’s get to the vulnerability. Bash is great for accessing computers remotely because it’s text-only. If you have a keyboard, you’re good to go. But that also potentially makes it easy for a malicious hacker to remotely access computers that she shouldn’t. If there’s a vulnerability in Bash, she can exploit it. And there is.
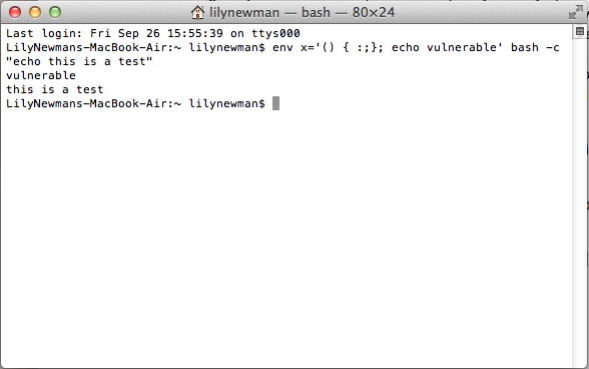
Essentially, the bug comes from how Bash handles what are called “environmental variables.” If you know about the vulnerability, you can trick Bash into executing commands that it shouldn’t even be registering as commands. The malicious command can be sort of tucked into text that Bash should ignore. And it can direct a computer to download malware or wreak all kinds of havoc.
The reason it’s important to understand what Unix and Bash are is so you can begin to grasp how widely Bash is distributed. It’s the default Unix shell command line processor in OS X, Linux, and other operating systems. It’s not used in most Microsoft software—so the Windows operating systems and websites built with Microsoft tools should be safe from this vulnerability. But Bash has been around since 1989, so it’s in a lot of devices.
Even worse in terms of controlling this bug, Bash is used on the Internet by software that automatically interacts with other programs in certain prescribed situations. For example, there’s no human involved when a website queries a server for updated content.
At this point, patches are available for Unix and Linux. Apple is presumably scrambling to deliver one as well. In a statement to iMore, an Apple representative said, “The vast majority of OS X users are not at risk to recently reported bash vulnerabilities. … With OS X, systems are safe by default and not exposed to remote exploits of bash unless users configure advanced Unix services.”
Even so, sites like Ars Technica and Krebs on Security are reporting evidence that hackers were exploiting the bug before it was discovered and that new ones are jumping on the bandwagon every moment. And it seems likely that someone, or lots of people, will create worms that exploit the bug and spread between vulnerable computers. Lovely.
People have been saying that Shellshock—named because it’s a vulnerability in a Unix shell, but you probably already figured that out—is a bigger bug than Heartbleed. One reason it seems like such a daunting problem is that much of the vulnerable software lives out of public sight. With Heartbleed, we could all take action. We waited for websites to patch the bug, and then we changed our passwords. But unless you are a router manufacturer or run a server farm, you may not know how to go about helping. And you may not be able to at all.
To give you a sense of how concerned people are, Robert Graham of Errata Security wrote that the bug can hide “deep within a website.” And Rich Mogull, the CEO of the cybersecurity firm Securosis, told Ars Technica that:
Bash is embedded and accessed in so many ways that we cannot fully understand its depth of use. Many systems you would never think of as having a command line use bash to run other programs. … We cannot possibly understand all the ways an attacker could interact with Bash to exploit this vulnerability.
Well, crap.
So what’s gonna happen now? Servers and embedded devices will increasingly receive patches that eliminate the threat, but it will take a long time before Shellshock is a nonissue because Bash has just been around for so long. It’s everywhere. For individuals, take you for example, the threat is probably fairly low, but there could be flare-ups where a trove of data gets compromised or personal accounts are accidentally exposed to malware because of Shellshock.
And if you’re just feeling fed up with all of these vulnerabilities, steel yourself and keep in mind what Slate’s Bitwise writer David Auerbach wrote after the discovery of Heartbleed: “Are there other zero-day bugs in … core infrastructure like Apache or BIND? Almost certainly.”