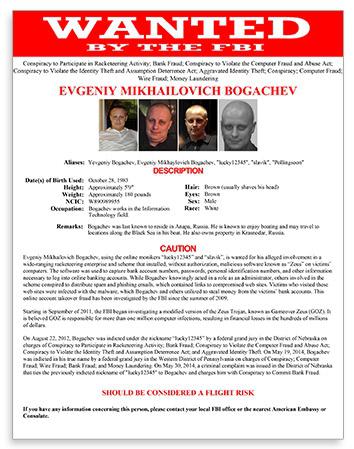
Law enforcement authorities took down the computer networks operating two major pieces of malware this weekend, and in the process added a new name to the FBI’s most wanted list of cybercriminals: Russian hacker Evgeniy Bogachev. Bogachev, the authorities believe, was responsible for operating both viruses and using them to steal millions of dollars. One of the viruses, GameOver Zeus, was able to capture banking credentials and then authorize transfers from their accounts. The other, a ransomware trojan called CryptoLocker, encrypted the files of computers it infected and then demanded payment to decrypt them. Together, GameOver Zeus and CryptoLocker have infected hundreds of thousands of machines.
The court documents concerning the operation make clear just how much work went into figuring out how to stop these viruses and, surprisingly, how much of law enforcement’s success was due not just to savvy technical hacking but also to old-fashioned sleuthing.
Why is it so hard to track down the servers—to say nothing of the people—responsible for operating these viruses? One reason is that there are so many layers of intermediaries between the victims and the perpetrators. Machines infected with GameOver Zeus (GOZ) did not report directly to a single command-and-control server, in the manner of traditional botnets, but instead operated on a peer-to-peer architecture in which they maintained connections to other infected machines, some of which served as intermediate “proxy nodes,” relaying commands from GOZ operators and sending encrypted data back to their “master drop” servers.
So the GOZ operators were not in direct communication with most of the infected machines and, similarly, they were not the direct recipients of the money transfers made using the stolen credentials. Instead, they recruited money mules via spam emails. (Sample text, from the FBI investigation: “If you are taking a career break, are on a maternity leave, recently retired or simply looking for some part-time job, this position is for you.” Imagine, for a moment, one of the largest cybercrime operations in the world being powered by postpartum mothers and aging retirees sitting at home on their laptops, waiting for million-dollar transfers to appear in their bank accounts …) These mules would receive the wire transfers directly from the victims’ accounts, keep a sum as their payment (“Starting salary is $2000 per month plus commission, paid every month”), and send the rest along to another account, presumably belonging to the GOZ operators.
Thus, Bogachev and his co-conspirators put several layers of computers and people between themselves and their crimes. And they also designed some phenomenally sophisticated software—GOZ, for instance, was even able to get into bank accounts protected with two-factor authentication by using a man-in-the-middle attack. Two-factor authentication works by requiring users to provide both a password and another credential, usually a code texted to their phone or stored on a physical token, in order to login. This way, even if a user’s password is stolen—or guessed—attackers still can’t login because they also need the phone or token belonging to that user to get the second factor. But GOZ was able to intercept these codes before they were used. Victims would enter their second authentication code, sent via text or physical token, into a fake login field (which they believed was actually their bank’s login page). The attackers would then capture that code, along with a password, and use both credentials to access the accounts.
Since the millions of dollars being reaped by GOZ-driven thefts were apparently not enough, its operators also began using the virus to install CryptoLocker on already infected machines. CryptoLocker victims were given a 72-hour window to choose between losing all of their data to unbreakable encryption or paying several hundred dollars in bitcoin or anonymous prepaid cash vouchers to retrieve it. (And since the criminals suspected there was still more money to be made here, they then set up a customer service website to help people figure out how to pay their bitcoin ransoms.)
So what were the weak links in this ruthless and lucrative business?
The FBI’s account of its investigation begins with a server in the United Kingdom that they suspected was linked to GOZ operations. U.K. authorities provided the FBI with a copy of that server’s contents, which included a password-protected website called visitcoastweekend.com with a frequently-asked-questions page featuring a bizarre blend of corporate buzzwords and dastardly criminal conspiracy. The page, translated from Russian, stated:
Starting on September we are beginning to work through the panel where you now find yourselves. [Fraudulent] Money transfers and drop [money mule] managers are synchronizing their work through our panel, which enables a much greater optimization of the work process and increase in the productivity of our work. Starting from this moment, all drop [money mule] managers with whom we are working and all [fraudulent] money transferors who work with us are working through this panel. We wish you all successful and productive work.
This was a promising start, but the investigators needed more to conclusively link the site to GOZ. Fortunately, the site also included a detailed list of hundreds of financial transactions with dates, company names, amounts, and the type of transfer. The FBI then began the painstaking work of verifying that these transfers were indeed the work of the GOZ virus. For example, they interviewed representatives from a composite materials company in the Western District of Pennsylvania to confirm that a $198,234.03 wire transfer on Oct. 21, 2011, from a SunTrust Bank account, the details of which were listed in the visitcoastweekend.com ledger, was, in fact, due the result of credentials stolen from a GOZ-infected machine. “For all listed companies with respect to which the FBI manually reviewed information in the ledger and compared it to information from either field interviews or bank fraud reporting, the information was an exact match,” FBI special agent Elliott Peterson wrote in his court declaration.
Meanwhile, a “confidential human source” provided the FBI with an email address that was being used by one of the GOZ operators. With a search warrant, officers were then able to retrieve from a service provider all of the records related to that email address. These records included when the email account was accessed and from what IP addresses, as well as the name associated with the account: Evgeniy Bogachev. Cross-referencing the IP addresses used to access Bogachev’s email account with those used to access visitcoastweekend.com and a CryptoLocker command-and-control server (traced from the U.S. to the U.K. to Luxembourg), the investigators found that there was significant overlap, leading them to conclude that Bogachev was involved in both schemes. Moreover, the fact that he had high-level administrative access the GOZ server led them to believe he was “a leader of the GOZ conspiracy.”
The identification of Bogachev is no small feat, as underlined by the fact that, thus far, all the FBI knows about his co-conspirators is their online aliases (“Temp Special,” “Ded,” “Chingiz 911,” and “mr. kykypyky”), and an email address used by one of them. (Don’t respond if he writes to you offering part-time work.) Bogachev used his real name on the email account and didn’t mask his IP address so it was possible to trace him when he accessed the GOZ and CryptoLocker servers, landing him on the FBI Cyber’s Most Wanted page.
The work of tracking down Bogachev and the servers running the GOZ and CryptoLocker operations was largely low-tech: interviewing money mules and victims, cross-referencing lengthy data logs, combing through websites and hacker forums (and translating them from Russian). By contrast, the takedown efforts this weekend involved extensive technical expertise—much of which is redacted from the FBI’s public records—to cut off the communications between all of GOZ’s complicated layers of peer and proxy nodes while also seizing the servers issuing them commands, including machines in Canada, Ukraine, and Kazakhstan.
On top of that, law enforcement had to make sure that Bogachev and his associates would be unable to re-establish control over the infected machines through a new server, something which the malware is specifically designed to do by means of a domain generation algorithm (DGA), which generates 1,000 domain names every week—long strings of letters followed by one of six top level domains, either .com, .net, .org, .biz, .info, or .ru. Every week, every machine infected with GOZ will go through the list and try to contact each of the thousand domains until a connection is established. So if the attackers were able to take set up any one of those domains during the appropriate week, they would be able to re-establish communication with all of the infected machines and regain control of the bot, rendering the FBI’s efforts largely useless. Thanks to the DGA, bots like CryptoLocker and Goz are effectively cyber-hydras. Cut off one server and a thousand more grow back in its place. To combat this, the FBI reverse-engineered the DGA, so they would know which thousand domains were being selected every week, and then on May 28 acquired a temporary restraining order that required domain registries in the U.S. to redirect any attempts to contact those domains to a substitute, government-run server. The domains generated by the DGA with the .ru top-level domain are controlled by registries in Russia, so the U.S. has no jurisdiction to force them to redirect traffic. Instead, the restraining order required U.S. service providers to block any connection requests to the .ru domains generated by the DGA.
All in all, it’s a massive and multi-layered strike against every element of the infrastructure underlying GOZ and CryptoLocker, though it remains to be seen whether the FBI and its partners have successfully thought of, and blocked, every possible way for the bots to be resurrected. In the meantime, it certainly wouldn’t hurt to run a virus scan.
There are several important lessons to be gleaned—about human carelessness (for all his technical genius, Bogachev made some elementary mistakes, like not changing his IP address whenever he accessed visitcoastweekend.com), about the digital footprints we leave regardless of how hard we try to hide them (the chain of evidence pointing back to Bogachev is damning), about the value of technical and social and legal mechanisms (reverse-engineering the DGA, interviewing informants and victims, and obtaining the restraining order were all crucial), about the importance of international collaboration for fighting cybercrime (none of this would have been possible without extensive cooperation from the U.K., Luxembourg, and quite likely other countries as well), and also about the clever ways countries can leverage their own Internet infrastructure to shield themselves from online activity beyond their control (the FBI can’t redirect .ru servers, but it can block U.S. computers from accessing them). More than anything, perhaps, it’s a lesson in how smart and sophisticated and careful today’s cybercriminals are—and how today’s cybersleuths may still be just a bit—or byte—ahead of them.