You’ve just opened a Web page or clicked a link in an email when your computer’s desktop goes gray. A browser window pops up with the FBI logo in the top left corner. Below it is a live webcam feed with a picture of someone’s face. You try to click away but find that your browser is locked. With a start, you recognize the face staring at you from the screen: It’s you.
This isn’t the plot of a Japanese horror film. It’s a frightening form of malware called “ransomware” that has been seen with increasing frequency in recent months. No one knows exactly how many people have been hit with it, but security firm McAfee reports that it recorded more than 120,000 new samples in the second quarter of 2012, a fourfold increase from the same quarter last year.
There are many variants of ransomware, all of which begin by locking you out of your own machine. The next phase: trying to blackmail, intimidate, or otherwise spook you into forking over cash. You probably shouldn’t do it. But it’s easy to see why a lot of people do.
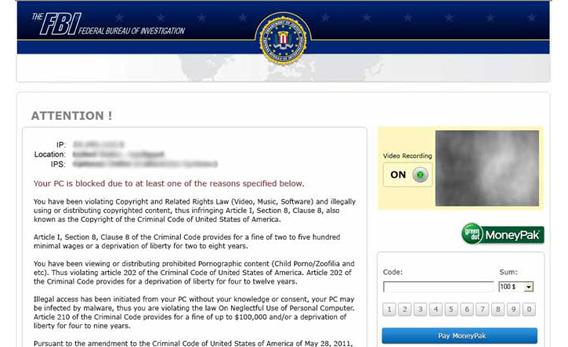
The version I described in the first paragraph is the product of a virus called Reveton, which you can contract either by clicking a malicious link or visiting an infected website, which triggers an automatic download. Beneath the video feed, which registers the surprise on your face as you recognize yourself, are your computer’s IP address and hostname and an urgent message: “Your computer has been locked!” Scroll further and you’ll find yourself accused of possessing illegally downloaded files in violation of federal copyright laws. (A new iteration claims that you’re in violation of SOPA, the Stop Online Piracy Act—which, as serious netizens know, never actually became law.)
The crime, you’re told, is punishable by a fine or up to three years in prison. There’s only one way to unlock your computer, according to the warning on your browser, and that’s to pay up. And if you don’t pay the specified “fine” within 48 or 72 hours—often by purchasing a prepaid cash card such as Green Dot’s Moneypak, which makes the transaction hard to trace—it claims that you’ll be locked out of your machine permanently and face criminal charges to boot.
The criminal charges are bogus, of course, but the threat of being permanently locked out of your files is real, says Chet Wisniewski, senior security adviser at the data-security firm Sophos. Some victims have reported that, after a certain amount of time passed, their files were in fact deleted. On the other hand, it’s unclear whether paying up actually helps, or if it just prompts the bad guys to try to squeeze more out of you. One thing security experts do know is that the scam appears to be automated. It would be a mistake to assume there’s an actual human on the other end whom you can persuade to take it easy on you because you really, really need those files.
Other types of ransomware do without the webcam scare tactic but ratchet up the stakes in other ways. Sophos’ Graham Cluley told me that his friend’s elderly parents were hit by a version that claimed to have found child pornography on their computer. They knew they hadn’t downloaded any such thing. Still, they were tempted to follow the instructions on screen rather than face the mortification of explaining the situation to their children or the police.
These scams represent an evolution from earlier forms of ransomware that made plain their creators’ criminal intentions. One variant reported by Sophos in 2010 would encrypt the users’ files, change their desktop wallpaper to an alert message, and then display a text file ordering them to send a $120 wire transfer to a Swiss bank account in exchange for instructions on decrypting their files. The alert warned users, “Don’t try to tell someone about this message if you want to get your files back!”
The scare tactics are clearly working. McAfee highlighted ransomware as one of the top malware trends in its latest quarterly threats report, noting that it seems to be replacing “fake AV,” or fake antivirus programs, as the scam du jour. (Fake AV reports peaked in mid-2011.) And Brian Krebs of the blog Krebs On Security got his hands on data from a ransomware scam in France that showed that, on one particular day, 2,116 PCs had been infected. Only 79 of the victims actually paid, but at $100 apiece, they provided a good haul for the hackers—especially considering they were doubtlessly running the same scam in many other countries.
What the ransomware wave demonstrates is that as the average computer user becomes wise to old tricks like the Nigerian email scam, criminal hackers will develop more sophisticated schemes. “Hacktivist” groups such as Anonymous and LulzSec get more press with their flashy denial-of-service attacks and password leaks targeting major corporations and government websites. But sprawling criminal networks, many with roots in Eastern Europe, quietly prey on individuals around the world on a daily basis.
So what should you do if you’re unwary and unlucky enough to contract a ransomware Trojan? First, instructs Sophos’ Paul Ducklin in a helpful video, don’t panic and don’t do anything rash. Once the malware has control of your machine, chances are that most of the damage has already been done. (In theory the hackers could mine your files for private information, but in practice they rarely do. Too much effort for an uncertain reward.) And ignore those threats not to tell anyone about the attack. Unless you’re an expert yourself, it’s absolutely a good idea to enlist the help of a computer security expert to help you figure out how to handle it. There’s a chance that an antivirus program could do the trick, but in most cases, you’ll have to reinstall your operating system from the ground up. The FBI—the real FBI—also recommends filing a complaint at www.ic3.gov.
As with most forms of malware, the best protection here is simply to avoid visiting compromised websites or clicking on any suspicious-looking links, whether on the Web or in emails, Twitter or Facebook messages, or even (lately) Skype messages. Keeping your operating system and apps updated with the latest security patches always helps, and antivirus software can be an additional prophylactic. But this particular type of attack also reinforces the importance of backing up your files. Otherwise, you might never see them again.
It’s conceivable, some security types admit privately, that paying up could prompt the criminals to restore them. But the official advice is that you never should, and in most cases that’s the advice that makes the most sense. Once the hackers have your money, there’s little incentive for them to restore your files. And seeing that they’ve found a sucker, they might come right back and target you again.