This piece is excerpted from Cybersecurity and Cyberwar: What Everyone Needs to Know, by Peter W. Singer and Allan Friedman, published by Oxford University Press.
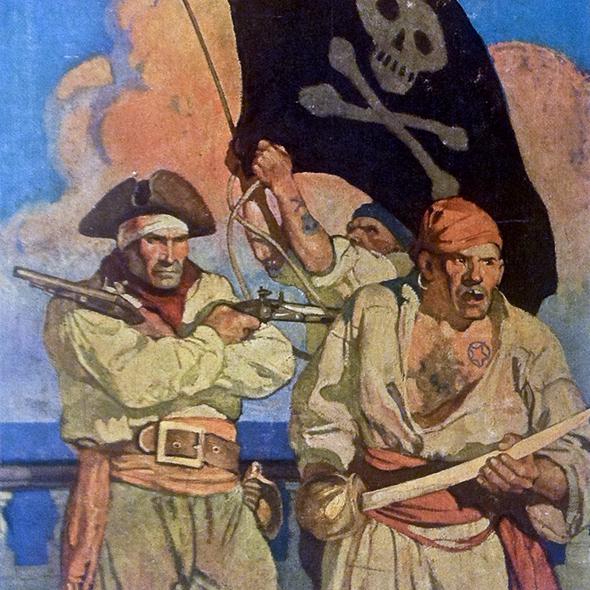
In 1522, three Spanish galleons left Havana, Cuba, on their way to Seville, Spain. Loaded onto the ships were literally tons of gold, emeralds, jade, and pearls, all the riches of the Aztec empire gathered into one massive shipment. Hernando Cortés has just conquered Mexico and was sending its treasure as a tribute back to his king, Charles V. But once the fleet set out on its long journey, five more ships appeared on the horizon. The lumbering treasure-laden ships couldn’t escape. A short fight ensued, and the Spanish lost to a squadron led by a French captain named Jean Fleury. By stealing the Aztec gold, Fleury had pulled the ultimate score. The episode would inspire generations to come and launch what is known as the “Golden Age of Piracy,” a period romanticized in books like Treasure Island and movies like Pirates of the Caribbean.
In centuries past, the sea was a primary domain of commerce and communication over which no one actor could claim complete control, much like the Internet today. While most just used the sea for normal commerce and communication, there were also those who engaged in bad deeds, again much like the Internet today. They varied widely, from individual pirates to state militaries with a global presence. In between were state-sanctioned pirates, known as privateers. Parallel to today’s “patriotic hackers” (or the private contractors working for government agencies like the National Security Agency or Cyber Command), privateers were not formally part of the state but licensed to act on its behalf. They were used both to augment traditional military forces and to add challenges of identification (attribution in cyber parlance) for those defending far-flung maritime assets.
These pirates and privateers would engage in various activities with cyber equivalents, from theft and hijacking, to blockades of trade (akin to a “denial of service”), to actual assaults on economic infrastructure and military assets. During the War of 1812, for example, the American privateer fleet numbered more than 517 ships—compared to the U.S. Navy’s 23. Even though the British conquered and burned the American capital city, the private American fleet caused such damage to the British economy that they compelled negotiations. As in cyberspace today, one of the biggest challenges for major powers was that an attacker could quickly shift identity and locale, changing its flags and often taking advantage of third-party harbors with loose local laws.
Maritime piracy is still with us, but it’s confined off the shores of failed states like Somalia and occurs on a miniscule scale compared to its golden age. (Only 0.01 percent of global shipping is taken by modern-day pirates.) Privateering, the parallel to the most egregious attacks we have seen in the cyber realm, is completely taboo. Privateers may have helped the U.S. against the British in the War of 1812, but by the time the American Civil War started in 1861,
President Lincoln not only refused to recruit plunderers-for-hire but also blasted the Confederates as immoral for opting to employ them.
The way this change came about provides an instructive parallel to explore for cybersecurity today. Much like the sea, cyberspace can be thought of as an ecosystem of actors with specific interests and capacities. Responsibility and accountability are not natural market outcomes, but incentives and frameworks can be created either to enable bad behavior or to support the greater public order.
To clamp down on piracy and privateering at sea, it took a two-pronged approach that went beyond just shoring up defenses or threatening massive attack (which are too often talked about in cybersecurity as the only options, again making false comparisons to the worst thinking of the Cold War). The first strategy was to go after the underlying havens, markets, and structures that put the profits into the practice and greased the wheels of bad behavior. Major markets for trading pirate booty were disrupted and shut down; pirate-friendly cities like Port Royal, Jamaica, were brought under heel, and blockades were launched on the potentates that harbored the corsairs of the southern Mediterranean and Southeast Asia.
Today, there are modern cyber equivalents to these pirate havens and markets. And much like the pirate-friendly harbors of old, a substantial portion of those companies and states that give cybercrime a legal free pass are known. These range from known malware and other cyber black marketplaces to the 50 Internet service providers that account for around half of all infected machines worldwide. Without the support of these havens and networks, online criminal enterprises would find it harder to practice their illegal action, which not only would clean the cyber seas, but also make it easier to identify and defend against the more serious attacks on infrastructure and the like.
Melissa Hathaway, who led the White House’s policy team on cyberspace issues, has talked about this as a strategy to “ ‘drain the swamp’ of malicious cyber activity and tilt the playing field [back] in our favor.” Much as with piracy at sea, some of the efforts might be taken as part of a cooperative global effort, while other actions could be taken on a unilateral basis, such as operations to disrupt or destroy the markets where hacker tools are traded, and tracking and targeting the assets of attackers themselves.
This links to the second strategy, the building of a network of treaties and norms, something explored in a following section. Fleury’s attack launched a golden age of piracy that was great for the pirates but not everyone else, including the governments of the time. Pirates, who had been tolerated at the individual level, began to be seen as general threats to economic prosperity. In turn, privateers, who had been viewed as useful tools, turned into the bureaucratic rivals of the formal navies being built up in these states (here again, akin to how patriotic hackers lose their shine when states build out more of their own formal cyber military units). As Janice Thompson recounts in her seminal study of why the pirate trade ended, Mercenaries, Pirates, and Sovereigns, maritime hijackers (and their state-approved counterparts) became marginalized as nations’ values changed and they saw the need to assert greater power and control.
Soon a webwork of agreements was established that set a general principle of open trade across the high seas. The agreements, some bilateral and others multilateral, also asserted that maritime sovereignty would only be respected when a nation took responsibility for any attacks that emanated from within its borders. Slowly, but surely, they paved the way toward a global code of conduct. By 1856, 42 nations agreed to the Declaration of Paris, which abolished privateering and formally turned pirates from accepted actors into international pariahs to be pursued by all the world’s major powers.
The cyber parallel today, again, is that all netizens have a shared global expectation of freedom of action on the Internet, particularly online trade, just as it is ensured on the open ocean. If you knowingly host or abet maritime pirates or privateers, their actions reflect back on you. The same should be true online. Building those norms will motivate both states and companies to keep a better check on individual hackers and criminals (the pirate equivalent). It will also weaken the value of outsourcing bad action to patriotic hackers (the latter-day privateers).
In addition to encouraging new accountability, this approach also offers opportunities for what are known as “confidence-building measures,” where two states that don’t get along can find ways to work together and build trust. After the War of 1812, for example, the British Royal Navy and nascent U.S. Navy constantly prepared for hostilities against each other, which made sense since they had just fought two outright wars. But as the network of norms began to spread, they also began to cooperate in anti-piracy and anti-slavery campaigns. That cooperation did more than underscore global norms: It built familiarity and trust between the two forces and helped mitigate the danger of military conflict during several crises. Similarly, today the United States and China are and will certainly continue to bolster their own cyber military capabilities. But like the Royal Navy and new American Navy back in the 1800s, this should not be a barrier to building cooperation. Both countries, for instance, could go after what the Chinese call “double crimes,” those actions in cyberspace that both nations recognize as illegal.
The lesson here is that the world is a better place with commerce and communication made safe and freewheeling pirates and privateers brought under control. Indeed, the period was never all that good even for the pirates. Jean Fleury made away with all that Aztec gold, but he should have quit while he was ahead. Just five years after the ultimate pirate score, he was caught by the Spanish on another raiding expedition and hanged.
For more information about Cybersecurity and Cyberwar: What Everyone Needs to Know, please visit www.cybersecuritybook.com.